Disclaimer: I’m not going into details on every step since I’m not writing a tutorial but mostly I’d like to prove that threats are getting more and more complex on relatively short time and that attack path is quite unique at least for my personal experience.
Everything started with an email attachment. “Nuovo Documento.doc” is its name and it is able to bypass every single AntiSpam and AntiMalware engine the target had. The following image shows the initial stage where the “.DOC” file seems to be benign but not compatible with the running Microsoft Word instance.
 |
| MalHide Sample as it looks like on opening. Stage 1 |
The sample presents some macro functions on it. Many junk functions have been injected on the VBA side in order to make life harder to reverse engineers, but fortunately, the great Microsoft VBA Editor included in the Microsoft Office suite implements a useful debugger. The analyst observes that the AutoOpen() function is preserved and filled by code. It took almost 3 seconds to figure out it was a malicious code. The following image shows the Microsoft VBA Editor debugging view where is possible to appreciate the variable qZbTUw containing a PowerShell encoded code. Here we are! The second stage is approaching the victim.
 |
| Stage 2. A running instance of PowerShell invoked by VBA |
The PowerShell code was Base64 Encoded and additionally obfuscated through “variable mess”. This technique is quite common for javascript devs since the code they develop runs on client side and obfuscating code is used technique to protect (sort of) the written code, but on the given scenario it looks like a simple implementation of FileLess Staging, where the attacker runs a
PowerShell script directly from memory without saving it on HD, in such a way the victim does not need to enable the “running PowerShell from file” Microsoft register key and it’s much harder from AntiVirus detect the infection stage. Then the script fires it on following the infection. Powershell ISE helps us to reverse the dropped payload. The following images show the decoding process: from the single line of obfuscated code to dropping URLs. I know, it’s almost impossible to see the images since they look like small, but please click on them to make a bigger view, if you wish.
 |
| Stage 3. Decoding Powershell Drop-and-Execute |
 |
| Stage 3. Decoded Powershell Drop-and-Execute |
The analyst is now able to identify the dropping websites and block them (please refer to IoC section)! The executed actions are quite standard. From an array of dropping website lets cycle over them and take the one who drops! The cycling policy could differ from sample to sample since they could use a pseudo-random seed generator or adopting an increment rotation or a round robin rotation and son. For this analysis is not interesting cycling policy at all since we decoded all the possible dropping files. The Powershell command gets the 52887.exe from an external source (dropping websites) and places it on C:\Users\Public\52887.exe. Finally, it runs it. Stage 4 has began, a new PE sample has been executed. The following image shows the Stage 4 dropping another stage into C:\Windows\SysWOW64\fonduewwa.exe. Fortunately, this stage drops the code from itself without getting on the network side. The fonduewwa.exe is then executed.
 |
| Stage 4. 52887.exe dropping to C:\Windows\SysWOW64\fonduewwa.exe |
The new stage (Stage 4) performs the following steps:
1) It fires up services which act as SMTP client.
2) Connects to a Command and Control which provides emails addresses, SMTP relays, and eMails body to be sent.
3) Sends eMail to exploit BeC communications.
The following images show the Command and Control address. The first image shows the used Windows API while the second one addresses the opened connections directly on the infected machine.
 |
| Command and Control IP Address (click to make it bigger) |
 |
| Command and Control DNS resolution (click to make it bigger) |
The Command and Control (c2) listen to: c-67-176-238-209.hsd1.il.comcast.net which today resolves in: 67.176.238.209. The C2 seems to answers to http queries having a specific set of cookies as the following image shows. The C2 crafted and rebuilt communication, made possible by reconstructing cookies from sniffed internal communications, gets back from C2 a kB of encoded data.
 |
| Command and Control Communication through HTTP |
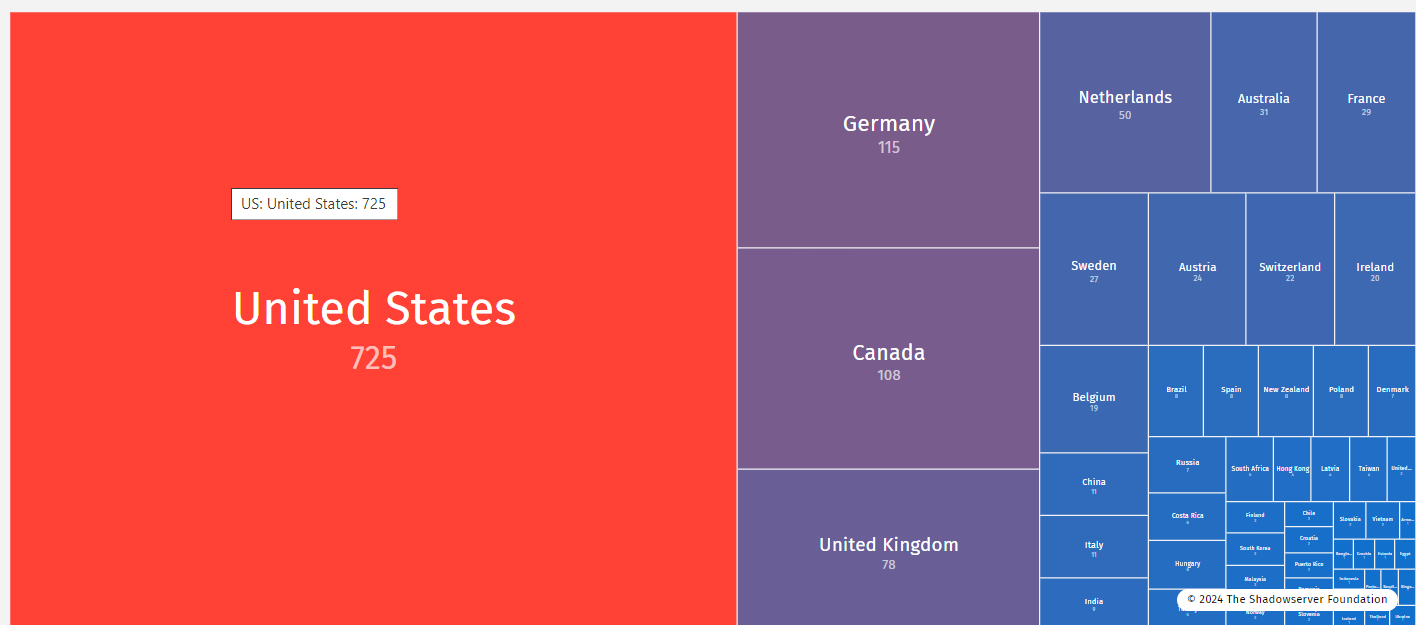
From C2 comes actions, victims addresses, SMTP servers, and passwords. The sample connects to a given SMTP relays, it authenticates itself and sends email to the victims. The following images prove that the attackers have plenty of credentials to SMTP relays around the globe.
 |
| MalHide Connection to real SMTP relays |
As now I will not disclose Username e Password for getting access to SMTP relays, but if you can prove to be the owner (or at least to be working for the company owning) of one of them let’s have a chat on that, many interesting things are happening into your network. The emails sent from the analyzed sample are targeting specific victims. It was pretty easy to figure out that we were facing a new attack vector! This attack vector looks like a
BeC (or CEO Scam) to specific targets. For those of you not familiar with this attack I am copying the definition provided by SANS (
here).
“Cyber criminals have developed a new attack called CEO Fraud, also known as Business Email Compromise (BEC). In these attacks, a cyber criminal pretends to be a CEO or other senior executive from your organization. The criminals send an email to staff members like yourself that try to trick you into doing something you should not do. These types of attacks are extremely effective because the cyber criminals do their research. They search your organization’s website for information, such as where it is located, who your executives are, and other organizations you work with. The cyber criminals then learn everything they can about your coworkers on sites like LinkedIn, Facebook, or Twitter. Once they know your organization’s structure, they begin to research and target specific employees. They pick their targets based on their specific goals. If the cyber criminals are looking for money, they may target staff in the accounts payable department. If they are looking for tax information, they may target human resources. If they want access to database servers, they could target someone in IT.Once they determine what they want and whom they will target, they begin crafting their attack. Most often, they use spear phishing. Phishing is when an attacker sends an email to millions of people with the goal of tricking them into doing something, for example, opening an infected attachment or visiting a malicious website. Spear phishing is similar to phishing; however, instead of sending a generic email to millions of people, they send a custom email targeting a very small, select number of people. These spear phishing emails are extremely realistic looking and hard to detect. They often appear to come from someone you know or work with, such as a fellow employee or perhaps even your boss. The emails may use the same jargon your coworkers use; they may use your organization’s logo or even the official signature of an executive. These emails often create a tremendous sense of urgency, demanding you take immediate action and not tell anyone.”
Following few examples of the sent emails coming from C2 and delivering through the analyzed MalHide sample.
Here we are, another email has been sent, another Malware has been thought and developed, another analysis I’ve been made but this time it looks like the “Malware economy” is seriously moving to fraud, there is much money respect to information stealing which is an ancient and romantic way to attack victims. Is this attack a significative example expressing the will of the new underground economy? Is this attack a small and silent change of paradigm, where previously the attacker was interested in your data in order to sell them but now he gets more interested on fraud third parties (such as companies) through you? I do not have such answer here.
Ok, now it’s time to explain why I called this Malware MalHide. Well, it’s a complex Malware, it hides several times BUT most important it has been developed to hide the attacker from sending emails in a way that is not possible to trace back the Attacker IP from the attack path. So I believe MalHide would be a nice name 😀
Further details on the MalHide malware, including the IoCs are reported in the original analysis published by Marco Ramilli
https://marcoramilli.blogspot.it/2018/05/malhide-interesting-malware-sample.html










 I do have experience on security testing since I have been performing penetration testing on several US electronic voting systems. I’ve also been encharged of testing uVote voting system from the
I do have experience on security testing since I have been performing penetration testing on several US electronic voting systems. I’ve also been encharged of testing uVote voting system from the