April 19, 2024
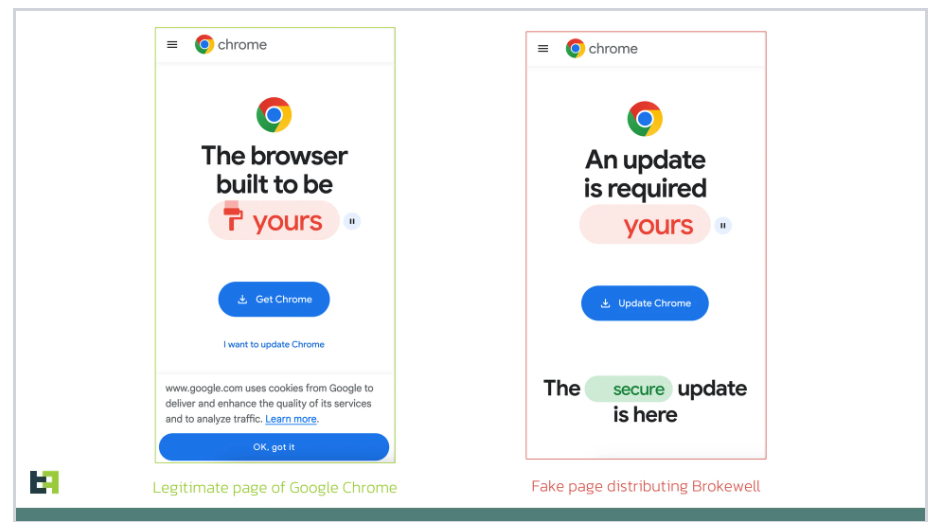
ThreatFabric researchers identified a new Android malware called Brokewell, which implements a wide range of device takeover capabilities. ThreatFabric researchers uncovered a new mobile malware n ...
A critical vulnerability in the WordPress Automatic plugin is being exploited to inject backdoors and web shells into websites WordPress security scanner WPScan warns that threat actors are exploi ...
As cryptocurrencies have grown in popularity, there has also been growing concern about cybercrime involvement in this sector Cryptocurrencies have revolutionized the financial world, offering new ...
Healthcare service provider Kaiser Permanente disclosed a security breach that may impact 13.4 million individuals in the United States. Kaiser Permanente is an American integrated managed care ...
November 16, 2023
November 16, 2023
November 14, 2023
ThreatFabric researchers identified a new Android malware called Brokewell, which implements a wide range of device takeover capabilities. ThreatFabric researchers uncovered a new mobile malware n ...
A critical vulnerability in the WordPress Automatic plugin is being exploited to inject backdoors and web shells into websites WordPress security scanner WPScan warns that threat actors are exploi ...
As cryptocurrencies have grown in popularity, there has also been growing concern about cybercrime involvement in this sector Cryptocurrencies have revolutionized the financial world, offering new ...
Healthcare service provider Kaiser Permanente disclosed a security breach that may impact 13.4 million individuals in the United States. Kaiser Permanente is an American integrated managed care ...
Over 1,400 CrushFTP internet-facing servers are vulnerable to attacks exploiting recently disclosed CVE-2024-4040 vulnerability. Over 1,400 CrushFTP internet-facing servers are vulnerable to attac ...
A ransomware attack on a Swedish logistics company Skanlog severely impacted the country's liquor supply. Skanlog, a critical distributor for Systembolaget, the Swedish government-owned retail c ...
CISA adds Cisco ASA and FTD and CrushFTP VFS vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the following v ...
U.S. CISA added the Windows Print Spooler flaw CVE-2022-38028 to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the CVE-2022-3 ...
The U.S. Department of Justice (DoJ) announced the arrest of two co-founders of a cryptocurrency mixer Samourai. The U.S. Department of Justice (DoJ) has arrested two co-founders of the cryptocur ...
Google addressed a critical Chrome vulnerability, tracked as CVE-2024-4058, that resides in the ANGLE graphics layer engine. Google addressed four vulnerabilities in the Chrome web browser, includ ...
Nation-state actor UAT4356 has been exploiting two zero-days in ASA and FTD firewalls since November 2023 to breach government networks. Cisco Talos warned that the nation-state actor UAT4356 (aka ...
A malware campaign has been exploiting the updating mechanism of the eScan antivirus to distribute backdoors and cryptocurrency miners. Avast researchers discovered and analyzed a malware campaign ...
The Treasury Department's Office of Foreign Assets Control (OFAC) sanctioned four Iranian nationals for their role in cyberattacks against the U.S.. The U.S. Treasury Department's Office of Foreig ...
A cyber attack on Leicester City Council resulted in certain street lights remaining illuminated all day and severely impacted the council's operations The Leicester City Council suffered a cybe ...
The National Police Agency in South Korea warns that North Korea-linked threat actors are targeting defense industry entities. The National Police Agency in South Korea warns that North Korea-link ...
The U.S. Department of State imposed visa restrictions on 13 individuals allegedly linked to the commercial spyware business. The US Department of State is imposing visa restrictions on 13 individ ...
A cyber attack has been disrupting operations at Synlab Italia, a leading provider of medical diagnosis services, since April 18. Since April 18, Synlab Italia, a major provider of medical diagno ...
Russia-linked APT28 group used a previously unknown tool, dubbed GooseEgg, to exploit Windows Print Spooler service flaw. Microsoft reported that the Russia-linked APT28 group (aka “Forest Blizz ...
A financially motivated group named GhostR claims the theft of a sensitive database from World-Check and threatens to publish it. World-Check is a global database utilized by various organizations ...
Japan's CERT warns of a vulnerability in the Forminator WordPress plugin that allows unrestricted file uploads to the server. Japan's CERT warned that the WordPress plugin Forminator, developed b ...
Government agencies revealed that Akira ransomware has breached over 250 entities worldwide and received over $42 million in ransom payments. A joint advisory published by CISA, the FBI, Europol, ...
Threat actors target government entities in the Middle East with a new backdoor dubbed CR4T as part of an operation tracked as DuneQuixote. Researchers from Kaspersky discovered the DuneQuixote ca ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Threat actors exploited a critical zero-day vulnerability in the CrushFTP enterprise in targeted attacks, Crowdstrike experts warn. CrushFTP is a file transfer server software that enables secure ...
A French hospital was forced to return to pen and paper and postpone medical treatments after a cyber attack. A cyber attack hit Hospital Simone Veil in Cannes (CHC-SV) on Tuesday, impacting med ...
The MITRE Corporation revealed that a nation-state actor compromised its systems in January 2024 by exploiting Ivanti VPN zero-days. In April 2024, MITRE disclosed a security breach in one of its ...
China-linked threat actors are preparing cyber attacks against U.S. critical infrastructure warned FBI Director Christopher Wray. FBI Director Christopher Wray warned this week that China-linked t ...
The United Nations Development Programme (UNDP) has initiated an investigation into an alleged ransomware attack and the subsequent theft of data. The United Nations Development Programme (UNDP) i ...
BlackBerry reported that the financially motivated group FIN7 targeted the IT department of a large U.S. carmaker with spear-phishing attacks. In late 2023, BlackBerry researchers spotted the thre ...
An international law enforcement operation led to the disruption of the prominent phishing-as-a-service platform LabHost. An international law enforcement operation, codenamed Nebulae and coordin ...
Russia-linked APT Sandworm employed a previously undocumented backdoor called Kapeka in attacks against Eastern Europe since 2022. WithSecure researchers identified a new backdoor named Kapek ...
Cisco has addressed a high-severity vulnerability in its Integrated Management Controller (IMC) for which publicly available exploit code exists. Cisco has addressed a high-severity Integrated Man ...
Threat actors are exploiting the CVE-2023-22518 flaw in Atlassian servers to deploy a Linux variant of Cerber (aka C3RB3R) ransomware. At the end of October 2023, Atlassian warned of a critical ...
Ivanti addressed two critical vulnerabilities in its Avalanche mobile device management (MDM) solution, that can lead to remote command execution. Ivanti addressed multiple flaws in its Avalanche ...
Researchers released an exploit code for the actively exploited vulnerability CVE-2024-3400 in Palo Alto Networks' PAN-OS. Researchers at watchTowr Labs have released a technical analysis of the ...
Cisco Talos warns of large-scale brute-force attacks against a variety of targets, including VPN services, web application authentication interfaces and SSH services. Cisco Talos researchers wa ...
The PuTTY Secure Shell (SSH) and Telnet client are impacted by a critical vulnerability that could be exploited to recover private keys. PuTTY tools from 0.68 to 0.80 inclusive are affected by a ...
Researchers warn of a renewed cyber espionage campaign targeting users in South Asia with the Apple iOS spyware LightSpy Blackberry researchers discovered a renewed cyber espionage campaign target ...
Amidst rising tensions with China in the SCS, Resecurity observed a spike in malicious cyber activity targeting the Philippines in Q1 2024. Amidst rising tensions with China in the South China Se ...
Czech transport minister warned that Russia conducted ‘thousands’ of attempts to sabotage railways, attempting to interfere with train networks and signals. Early this month, the Czech transpo ...
The Dark Angels (Dunghill) ransomware group claims the hack of the chipmaker Nexperia and the theft of 1 TB of data from the company. The Dark Angels (Dunghill) ransomware group claims responsibil ...
Cisco Duo warns that a data breach involving one of its telephony suppliers exposed multifactor authentication (MFA) messages sent by the company via SMS and VOIP to its customers. Cisco Duo war ...
The Ukrainian hacking group Blackjack used a destructive ICS malware dubbed Fuxnet in attacks against Russian infrastructure. Industrial and enterprise IoT cybersecurity firm Claroty reported that ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Palo Alto Networks PAN-OS Command Injection flaw to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infras ...
Threat actors have been exploiting the recently disclosed zero-day in Palo Alto Networks PAN-OS since March 26, 2024. Palo Alto Networks and Unit 42 are investigating the activity related to CVE-2 ...
A joint investigation conducted by U.S. and Australian authorities led to the arrest of two key figures behind the Firebird RAT operation. A joint law enforcement operation conducted by the Austra ...
A threat actor claimed the hack of the Canadian retail chain Giant Tiger and leaked 2.8 million records on a hacker forum. A threat actor, who goes online with the moniker ShopifyGUY, claimed re ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Researchers warn threat actors are manipulating GitHub search results to target developers with persistent malware. Checkmarx researchers reported that threat actors are manipulating GitHub search ...
A critical vulnerability, named ‘BatBadBut’, impacts multiple programming languages, its exploitation can lead to command injection in Windows applications. The cybersecurity researcher RyotaK ...
Roku announced that 576,000 accounts were compromised in a new wave of credential stuffing attacks. Roku announced that 576,000 accounts were hacked in new credential stuffing attacks, threat act ...
Crooks targeted a LastPass employee using deepfake technology to impersonate the company's CEO in a fraudulent scheme. In a fraudulent scheme, criminals used deepfake technology to impersonate Las ...
TA547 group is targeting dozens of German organizations with an information stealer called Rhadamanthys, Proofpoint warns. Proofpoint researchers observed a threat actor, tracked as TA547, targe ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds D-Link multiple NAS devices bugs to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Securit ...
Business intelligence software company Sisense suffered a cyberattack that may have exposed sensitive information of major enterprises worldwide. Sisense, a business intelligence software company, ...
Palo Alto Networks fixed several vulnerabilities in its PAN-OS operating system, including 3 issues that can trigger a DoS condition on its firewalls. Palo Alto Networks released security updates ...
Apple is warning iPhone users in over 90 countries of targeted mercenary spyware attacks, Reuters agency reported. Apple is alerting iPhone users in 92 countries about mercenary spyware attacks, r ...
Microsoft addressed two zero-day vulnerabilities (CVE-2024-29988 and CVE-2024-26234) actively exploited by threat actors to deliver malware Microsoft addressed two zero-day vulnerabilities, tracke ...
Group Health Cooperative of South Central Wisconsin disclosed a data breach that impacted over 500,000 individuals. The Group Health Cooperative of South Central Wisconsin (GHC-SCW) is a non-prof ...
AT&T confirmed that the data breach impacted 51 million former and current customers and is notifying them. AT&T revealed that the recently disclosed data breach impacts more than 51 milli ...
Fortinet addressed multiple issues in FortiOS and other products, including a critical remote code execution flaw in FortiClientLinux. Fortinet fixed a dozen vulnerabilities in multiple products, ...
Microsoft Patches Tuesday security updates for April 2024 addressed three Critical vulnerabilities, none actively exploited in the wild. Microsoft Patches Tuesday security updates for April 2024 a ...
As technology evolves and our dependence on digital systems increases, the cybersecurity threat landscape also rapidly changes, posing fresh challenges for organizations striving to protect their ass ...
Researchers found multiple vulnerabilities in LG webOS running on smart TVs that could allow attackers to gain root access to the devices. Bitdefender researchers discovered multiple vulnerabiliti ...
Researchers discovered a sophisticated multi-stage attack that leverages ScrubCrypt to drop VenomRAT along with many malicious plugins. Fortinet researchers observed a threat actor sending out a p ...
Google announced support for a V8 Sandbox in the Chrome web browser to protect users from exploits triggering memory corruption issues. Google has announced support for what's called a V8 Sandb ...
China-linked threat actors are using AI to carry out influence operations aimed at fueling social disorders in the U.S. and Taiwan. China is using generative artificial intelligence to carry out ...
Greylock McKinnon Associates, a service provider for the Department of Justice, suffered a data breach that exposed data of 341650 people. Greylock McKinnon Associates (GMA) provides expert econom ...
Zero-day broker firm Crowdfense announced a 30 million USD offer as part of its Exploit Acquisition Program. Crowdfense is a world-leading research hub and acquisition platform focused on high-qua ...
The U.S. Department of Health and Human Services (HHS) warns of attacks against IT help desks across the Healthcare and Public Health (HPH) sector. The U.S. Department of Health and Human Services ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
A researcher disclosed an arbitrary command injection and hardcoded backdoor issue in multiple end-of-life D-Link NAS models. A researcher who goes online with the moniker 'Netsecfish' disclosed a ...
Experts warn of roughly 16,500 Ivanti Connect Secure and Poly Secure gateways still vulnerable to a remote code execution (RCE) flaw. Shadowserver researchers reported that roughly 16,500 Ivanti C ...
Cisco warns customers of Small Business RV016, RV042, RV042G, RV082, RV320, and RV325 Routers Cross-Site scripting flaw. Cisco warns of a Small Business RV016, RV042, RV042G, RV082, RV320, and RV3 ...
Threat actors are exploiting critical Magento vulnerability CVE-2024-20720 to install a persistent backdoor on e-stores. Sansec researchers observed threat actors are exploiting the recently discl ...
US hotel chain Omni Hotels & Resorts suffered a cyber attack that forced the company to shut down its systems. A cyberattack hit Omni Hotels & Resorts disrupting its services and forcing t ...
HTTP/2 CONTINUATION Flood: Researchers warn of a new HTTP/2 vulnerability that can be exploited to conduct powerful denial-of-service (DoS) attacks. HTTP messages can contain named fields in both ...
US cancer center City of Hope suffered a data breach that impacted 800,000 individuals, personal and health information was compromised. City of Hope is a renowned cancer research and treatment ce ...
Ivanti addressed four flaws impacting Connect Secure and Policy Secure Gateways that could lead to code execution and denial-of-service (DoS) condition. Ivanti has released security updates to add ...
Jackson County, Missouri, confirmed that a ransomware attack has disrupted several county services. A ransomware attack disrupted several services of the Jackson County, Missouri. The County Execu ...
Google fixed another Chrome zero-day vulnerability exploited during the Pwn2Own hacking competition in March. Google has addressed another zero-day vulnerability in the Chrome browser, tracked as ...
Resecurity researchers warn that a new Version of JsOutProx is targeting financial institutions in APAC and MENA via Gitlab abuse. Resecurity has detected a new version of JSOutProx, which is targ ...
Google addressed several vulnerabilities in Android and Pixel devices, including two actively exploited flaws. Google addressed 28 vulnerabilities in Android and 25 flaws in Pixel devices. Two iss ...
Serious security breach hits EU police agency A batch of highly sensitive files containing the personal information of top Europol executives mysteriously disappeared last summer The website Po ...
A cross-site scripting vulnerability (XXS) in the WordPress WP-Members Membership plugin can lead to malicious script injection. Researchers from Defiant’s Wordfence research team disclosed a cr ...
Researchers from the firmware security firm Binarly released a free online scanner to detect the CVE-2024-3094 Backdoor Last week, Microsoft engineer Andres Freund discovered a backdoor issue in ...
Google is going to delete data records related to the 'Incognito Mode' browsing activity to settle a class action lawsuit. Google has agreed to delete billions of data records related to users' br ...
Threat actors claimed the hack of the PandaBuy online shopping platform and leaked data belonging to more than 1.3 million customers. At least two threat actors claimed the hack of the PandaBuy on ...
The OWASP Foundation disclosed a data breach that impacted some members due to a misconfiguration of an old Wiki web server. The OWASP Foundation has disclosed a data breach that impacted some of ...
Researchers detected a new version of the Vultur banking trojan for Android with enhanced remote control and evasion capabilities. Researchers from NCC Group discovered a new version of the Vultur ...
The US government announced establishing the Office of the Assistant Secretary of Defense for Cyber Policy. The US Defense Department announced establishing the Office of the Assistant Secretary o ...
Experts warn of info stealer malware, including Atomic Stealer, targeting Apple macOS users via malicious ads and rogue websites. Jamf Threat Labs researchers analyzed info stealer malware attack ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
A Linux variant of the DinodasRAT backdoor used in attacks against users in China, Taiwan, Turkey, and Uzbekistan, researchers from Kaspersky warn. Researchers from Kaspersky uncovered a Linux ...
AT&T confirmed that a data breach impacted 73 million current and former customers after its data were leaked on a cybercrime forum. In March 2024, more than 70,000,000 records from an unspeci ...
Red Hat warns of a backdoor in XZ Utils data compression tools and libraries in Fedora development and experimental versions. Red Hat urges users to immediately stop using systems running Fedora ...
The German Federal Office for Information Security (BSI) warned of thousands of Microsoft Exchange servers in the country vulnerable to critical flaws. The German Federal Office for Information Se ...
Cisco warns customers of password-spraying attacks that have been targeting Remote Access VPN (RAVPN) services of Cisco Secure Firewall devices. Cisco is warning customers of password-spraying att ...
Hot Topic suffered credential stuffing attacks that exposed customers' personal information and partial payment data. Hot Topic, Inc. is an American fast-fashion company specializing in counte ...
Cisco addressed multiple vulnerabilities in IOS and IOS XE software that can be exploited to trigger a denial-of-service (DoS) condition. Cisco this week released patches to address multiple IOS a ...
Google's Threat Analysis Group (TAG) and Mandiant reported a surge in the number of actively exploited zero-day vulnerabilities in 2023. Google's Threat Analysis Group (TAG) and its subsidiary Man ...
Google addressed two zero-day vulnerabilities in the Chrome web browser that have been demonstrated during the Pwn2Own Vancouver 2024. Google addressed several vulnerabilities in the Chrome web br ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a Microsoft SharePoint vulnerability disclosed at the 2023 Pwn2Own to its Known Exploited Vulnerabilities catalog. The U.S. Cybers ...
This is the advantage of Data Detection and Response (DDR) for organizations aiming to build a real-time data defense. In cybersecurity, and in life, by the time you find out that something went w ...
The Finnish Police attributed the attack against the parliament that occurred in March 2021 to the China-linked group APT31. The Finnish Police attributed the March 2021 attack on the parliament t ...
A new variant of TheMoon malware infected thousands of outdated small office and home office (SOHO) routers and IoT devices worldwide. The Black Lotus Labs team at Lumen Technologies uncovered an ...
UK, Australia and New Zealand are accusing China-linked threat actors of cyber operations against UK institutions and parliamentarians. GCHQ’s National Cyber Security Centre believes that China- ...
The US Treasury Department announced sanctions on two APT31 Chinese hackers linked to attacks against organizations in the US critical infrastructure sector. The US government announced sanctions ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds FortiClient EMS, Ivanti EPM CSA, Nice Linear eMerge E3-Series bugs to its Known Exploited Vulnerabilities catalog. The U.S. Cybers ...
In recent campaigns, Iran-linked APT group MuddyWater used a legitimate Remote Monitoring and Management (RMM) solution called Atera. Proofpoint researchers observed the Iran-linked APT group Mudd ...
Researchers reported that over 100 organizations in Europe and US were targeted by a wave of large-scale StrelaStealer campaigns Palo Alto Networks' Unit42 spotted a wave of large-scale StrelaStea ...
Researchers demonstrated a new side-channel attack, named GoFetch, against Apple CPUs that could allow an attacker to obtain secret keys. A team of researchers from several US universities demonst ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
During the month of Ramadan, Resecurity observed a significant increase in fraudulent activities and scams. During the month of Ramadan, Resecurity observed a significant increase in fraudulent ac ...
Russia-linked threat actors employ the WINELOADER backdoor in recent attacks targeting German political parties. In late February, Mandiant researchers spotted the Russia-linked group APT29 using ...
Mozilla addressed two Firefox zero-day vulnerabilities exploited during the Pwn2Own Vancouver 2024 hacking competition. Mozilla has done an amazing job addressing two zero-day vulnerabilities in t ...
A large-scale malware campaign, tracked as Sign1, has already compromised 39,000 WordPress sites in the last six months. Sucurity researchers at Sucuri spotted a malware campaign, tracked as Sign1 ...
The German police seized the infrastructure of the darknet marketplace Nemesis Market disrupting its operation. An operation conducted by the Federal Criminal Police Office in Germany (BKA) and th ...
A flaw in Dormakaba Saflok electronic locks, dubbed Unsaflok, can allow threat actors to open millions of doors worldwide. Researchers Lennert Wouters, Ian Carroll, rqu, BusesCanFly ...
Pwn2Own Vancouver 2024 hacking competition has ended, and participants earned $1,132,500 for demonstrating 29 unique zero-days. Trend Micro’s Zero Day Initiative (ZDI) announced that participant ...
Researchers released a PoC exploit for a critical flaw in Fortinet's FortiClient Enterprise Management Server (EMS) software, which is actively exploited. Security researchers at Horizon3 have rel ...
Participants earned $732,500 on the first day of the Pwn2Own Vancouver 2024 hacking competition, a team demonstrated a Tesla hack. Participants earned $732,000 on the first day of the Pwn2Own Vanc ...
Boffins devised a new application-layer loop DoS attack based on the UDP protocol that impacts major vendors, including Broadcom, Microsoft and MikroTik. Researchers from the CISPA Helmholtz Cente ...
Atlassian fixed tens of vulnerabilities in Bamboo, Bitbucket, Confluence, and Jira products, including a critical flaw that can be very dangerous. Atlassian addressed multiple vulnerabilities in i ...
Multiple threat actors are exploiting the recently disclosed JetBrains TeamCity flaw CVE-2024-27198 in attacks in the wild. Trend Micro researchers are exploiting the recently disclosed vulnerabil ...
Researchers found a new variant of the BunnyLoader malware with a modular structure and new evasion capabilities. In October 2023, Zscaler ThreatLabz researchers discovered a new malware ...
The Pokemon Company resets some users' passwords in response to hacking attempts against some of its users. The Pokemon Company announced it had reset the passwords for some accounts after it had ...
Ukraine cyber police, along with the national police, arrested three hackers attempting to sell 100 million compromised emails and Instagram accounts. The Ukraine cyber police and the national pol ...
A new variant of the Russia-linked wiper AcidRain, tracked as AcidPour, was spotted targeting Linux x86 devices. A new variant of a data wiper AcidRain, tracked as AcidPour, is specifically design ...
On Sunday, two competitive esports players were hacked while participating at the Apex Legends Global Series tournament. Electronic Arts postponed the North American (NA) finals of the Apex ...
Trend Micro uncovered a sophisticated campaign conducted by Earth Krahang APT group that breached 70 organizations worldwide. Trend Micro researchers uncovered a sophisticated campaign conducted b ...
Fortra addressed a critical remote code execution vulnerability impacting its FileCatalyst file transfer product. Fortra has released updates to address a critical vulnerability, tracked as CVE- ...
Technology giant Fujitsu announced it had suffered a cyberattack that may have resulted in the theft of customer information. Japanese technology giant Fujitsu on Friday announced it had suffered ...
A critical vulnerability in WordPress miniOrange's Malware Scanner and Web Application Firewall plugins can allow site takeover. On March 1st, 2024, WordPress security firm Wordfence received a su ...
Resecurity reported about the increasing wave of cyber incidents targeting the aerospace and aviation sectors. The experts emphasized the importance of rigorous cybersecurity risk assessments for ...
Threat actors compromised at least 11 International Monetary Fund (IMF) email accounts earlier this year, the organization revealed. The International Monetary Fund (IMF) disclosed a security brea ...
Researchers at vx-underground first noticed that more than 70,000,000 records from AT&T were leaked on the Breached hacking forum. More than 70,000,000 records from an unspecified division of ...
Cybersecurity researchers discovered multiple GitHub repositories hosting cracked software that are used to drop the RisePro info-stealer. G-Data researchers found at least 13 such Github reposito ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Unemployment agency France Travail (Pôle Emploi) recently suffered a data breach that could impact 43 million people. On August 2023, the French government employment agency Pôle emploi suffered ...
School districts continue to be under attack, schools in Scranton, Pennsylvania, are suffering a ransomware attack. This week, schools in Scranton, Pennsylvania, experienced a ransomware attack, r ...
North Korea-linked Lazarus APT group allegedly using again the mixer platform Tornado Cash to launder $23 million. North Korea-linked Lazarus APT group allegedly has reportedly resumed using the ...
US DoJ sentenced a Moldovan national (31) to 42 months in federal prison for operating the E-Root cybercrime marketplace. U.S. District Court sentenced the Moldovan national (31) Sandu Boris Diaco ...
Russian hackers have knocked down the GPS and communications of Defence Secretary Grant Shapps RAF Dassault Falcon 900 jet with electronic warfare attack. Defence Secretary Grant Shapps RAF Dassau ...
Cisco this week addressed high-severity elevation of privilege and denial-of-service (DoS) vulnerabilities in IOS RX software. Cisco addressed multiple vulnerabilities in IOS RX software, includin ...
Researchers recently uncovered a DarkGate campaign in mid-January 2024, which exploited Microsoft zero-day vulnerability. Researchers at the Zero Day Initiative (ZDI) recently uncovered a DarkGat ...
The ransomware attack that hit the systems of Nissan Oceania in December 2023 impacted roughly 100,000 individuals. Nissan Oceania, the regional division of the multinational carmaker, announced i ...
Researchers analyzed ChatGPT plugins and discovered several types of vulnerabilities that could lead to data exposure and account takeover. Researchers from Salt Security discovered three types of ...
Fortinet released security updates to address critical code execution vulnerabilities in FortiOS, FortiProxy, and FortiClientEMS. Fortinet this week has released security updates to fix critical c ...
Acer Philippines disclosed a data breach after employee data was leaked by a threat actor on a hacking forum. Acer Philippines confirmed that employee data was compromised in an attack targeting a ...
Threat actors behind the ransomware attacks that hit Stanford University in 2023 gained access to 27,000 people. Stanford University confirmed that threat actors behind the September 2023 ransomwa ...
Microsoft Patch Tuesday security updates for March 2024 addressed 59 security vulnerabilities in its products, including RCE flaws. Microsoft released Patch Tuesday security updates for March 2023 ...
Russia’s Foreign Intelligence Service (SVR) claims that the US intelligence plans to interfere with its presidential election. Russia's Foreign Intelligence Service (SVR) alleges that the US is ...
Russian authorities have detained a South Korean national on cyber espionage charges, it is the first time for a Korean citizen. Russian authorities have arrested a South Korean citizen on charges ...
Threat actors can abuse QR codes to carry out sophisticated scams, as reported by the Italian Postal Police in its recent alert. As is well known, QR codes are two-dimensional barcodes that can be ...
A series of “intense” cyberattacks hit multiple French government agencies, revealed the prime minister’s office. "Several "intense" cyberattacks targeted multiple French government agencies ...
BianLian ransomware group was spotted exploiting vulnerabilities in JetBrains TeamCity software in recent attacks. Researchers from GuidePoint Security noticed, while investigating a recent attack ...
Researchers released technical specifics and a PoC exploit for a recently disclosed flaw in Progress Software OpenEdge Authentication Gateway and AdminServer. Researchers from Horizon3.ai have pub ...
The financially motivated hacking group Magnet Goblin uses various 1-day flaws to deploy custom malware on Windows and Linux systems. A financially motivated threat actor named Magnet Goblin made ...
Threat actors are hacking WordPress sites by exploiting a vulnerability, tracked as CVE-2023-6000, in old versions of the Popup Builder plugin. In January, Sucuri researchers reported that Balada ...
A report published by Lithuanian security services warned that China has escalated its espionage operations against Lithuania. A report released by Lithuanian security services has cautioned that ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Threat actors hacked the systems of the Cybersecurity and Infrastructure Security Agency (CISA) by exploiting Ivanti flaws. The US Cybersecurity and Infrastructure Security Agency (CISA) agency wa ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a JetBrains TeamCity vulnerability to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Secur ...
Researchers warn that the critical vulnerability CVE-2024-21762 in Fortinet FortiOS could potentially impact 150,000 exposed devices. In February, Fortinet warned that the critical remot ...
QNAP addressed three vulnerabilities in its NAS products that can be exploited to access devices. QNAP addressed three vulnerabilities in Network Attached Storage (NAS) devices that can be exploit ...
Microsoft revealed that Russia-linked APT group Midnight Blizzard recently breached its internal systems and source code repositories. Microsoft published an update on the attack that hit the comp ...
Cisco addressed two high-severity vulnerabilities in Secure Client that could lead to code execution and unauthorized remote access VPN sessions. Cisco released security patches to address two hig ...
The ransomware attack on Xplain impacted tens of thousands Federal government files, said the National Cyber Security Centre (NCSC) of Switzerland. The National Cyber Security Centre (NCSC) publis ...
The FBI Internet Crime Complaint Center (IC3) 2023 report states that reported cybercrime losses reached $12.5 billion in 2023. The 2023 Internet Crime Report published the FBI's Internet Crime Co ...
The national intelligence agency of Moldova warns of hybrid attacks from Russia ahead of the upcoming elections. The Moldovan national intelligence agency warns of hybrid attacks from Russia ahead ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apple iOS and iPadOS memory corruption vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and ...
A new Linux malware campaign campaign is targeting misconfigured Apache Hadoop, Confluence, Docker, and Redis instances. Researchers from Cado Security observed a new Linux malware campaign target ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Android Pixel and Sunhillo SureLine vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Inf ...
Researchers warn that the cybercrime groups GhostSec and Stormous have joined forces in a new ransomware campaign. The GhostSec and Stormous ransomware gang are jointly conducting a ransomware cam ...
The wide torrent-based accessibility of these leaked victim files ensures the longevity of LockBit 3.0’s harmful impact. While embattled ransomware gang LockBit 3.0 fights for its survival follo ...
Apple released emergency security updates to address two new iOS zero-day vulnerabilities actively exploited in the wild against iPhone users. Apple released emergency security updates to address ...
VMware released urgent patches to address critical ESXi sandbox escape vulnerabilities in the ESXi, Workstation, Fusion and Cloud Foundation products Virtualization giant VMware released urgent up ...
The U.S. government sanctioned two individuals and five entities linked to the development and distribution of the Predator spyware used to target Americans. Today, the Department of the Treasury� ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a Microsoft Windows Kernel vulnerability to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure ...
Two new security flaws in JetBrains TeamCity On-Premises software can allow attackers to take over affected systems. Rapid7 researchers disclosed two new critical security vulnerabilities, tracked ...
The Main Intelligence Directorate (GUR) of Ukraine's Ministry of Defense claims that it hacked the Russian Ministry of Defense. The Main Intelligence Directorate (GUR) of Ukraine's Ministry of Def ...
American Express warns customers that their credit cards were exposed due to a data breach experienced by a third-party merchant processor. American Express (Amex) notifies customers that thei ...
This is my interview with TRT International on the Meta dispute with EU consumer groups, which are calling on the bloc to sanction the company EU consumer groups are calling on the bloc to sanctio ...
Researcher HaxRob discovered a previously undetected Linux backdoor named GTPDOOR, designed to target telecom carrier networks. Security researcher HaxRob discovered a previously undetected Linux ...
Threat actors stole sensitive and confidential data from the telecom giant Chunghwa Telecom Company, revealed the Ministry of National Defense. Chunghwa Telecom Company, Ltd. (literally Chinese Te ...
A new Linux variant of the remote access trojan (RAT) BIFROSE (aka Bifrost) uses a deceptive domain mimicking VMware. Palo Alto Networks Unit 42 researchers discovered a new Linux variant of Bifro ...
Camera doorbells manufactured by the Chinese company Eken Group Ltd under the brands EKEN and Tuck are affected by major vulnerabilities. Researchers from Consumer Reports (CR) discovered severe ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
A U.S. Court ordered surveillance firm NSO Group to hand over the source code for its Pegasus spyware and other products to Meta. Meta won the litigation against the Israeli spyware vendor NSO G ...
The U.S. DoJ charged Iranian national Alireza Shafie Nasab for his role in attacks targeting U.S. government and defense entities. The U.S. Department of Justice (DoJ) charged Iranian national Ali ...
US CISA, the FBI, and MS-ISAC issued a joint CSA to warn of attacks involving Phobos ransomware variants observed as recently as February 2024 US CISA, the FBI, and MS-ISAC issued a joint cyber se ...
German police seized the largest German-speaking cybercrime marketplace Crimemarket and arrested one of its operators. The Düsseldorf Police announced that a large-scale international law enforc ...
The Five Eyes alliance warns of threat actors exploiting known security flaws in Ivanti Connect Secure and Ivanti Policy Secure gateways. The Five Eyes intelligence alliance issued a joint cyberse ...
Crooks stole €15.5 million from the European variety retail and discount company Pepco through a phishing attack. The Hungarian business of the European discount retailer Pepco Group has been t ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds a Microsoft Streaming Service vulnerability to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastruct ...
A critical vulnerability in Facebook could have allowed threat actors to hijack any Facebook account, researcher warns. Meta addressed a critical Facebook vulnerability that could have allowed att ...
A new threat actor, tracked as dubbed SPIKEDWINE, has been observed targeting officials in Europe with a previously undetected backdoor WINELOADER. Zscaler researchers warn that a previously un ...
Experts warn that the LockBit ransomware group has started using updated encryptors in new attacks, after the recent law enforcement operation. The LockBit ransomware group appears to have fully r ...
North Korea-linked Lazarus APT exploited a zero-day flaw in the Windows AppLocker driver (appid.sys) to gain kernel-level access to target systems. Avast researchers observed North Korea-linked La ...
Pharmaceutical giant Cencora suffered a cyber attack and threat actors stole data from its infrastructure. Pharmaceutical giant Cencora disclosed a data breach after it was the victim of a cyberat ...
Analyzing the Email Security Landscape and exploring Emerging Threats and Trends. In the ever-shifting digital arena, staying ahead of evolving threat trends is paramount for organizations aiming ...
The FBI, CISA, and the Department of HHS warned U.S. healthcare organizations of targeted ALPHV/Blackcat ransomware attacks. A cybersecurity alert published by the FBI, CISA, and the Department of ...
Russian cyberspies are compromising Ubiquiti EdgeRouters to evade detection, warns a joint advisory published by authorities. The Federal Bureau of Investigation (FBI), National Security Agency (N ...
New threat actors have started exploiting ConnectWise ScreenConnect vulnerabilities, including the Black Basta and Bl00dy ransomware gangs. Multiple threat actors have started exploiting the recen ...
Researchers warn of an XSS vulnerability, tracked as CVE-2023-40000, in the LiteSpeed Cache plugin for WordPress Patchstack researchers warn of an unauthenticated site-wide stored XSS vulnerabilit ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
U.S. government offers rewards of up to $15 million for information that could lead to the identification or location of LockBit ransomware gang members and affiliates. The U.S. Department of Stat ...
A new malware campaign targets Redis servers to deploy the mining crypto miner Migo on compromised Linux hosts. Caro Security researchers have observed a new malware campaign targeting Redis serve ...
VMware urges customers to uninstall the deprecated Enhanced Authentication Plugin (EAP) after the disclosure of a critical flaw CVE-2024-22245. VMware is urging users to uninstall the deprecated E ...
Researchers from Shadowserver Foundation identified roughly 28,000 internet-facing Microsoft Exchange servers vulnerable to CVE-2024-21410. The vulnerability CVE-2024-21410 is a bypass vulnerabili ...
ConnectWise addressed two critical vulnerabilities in its ScreenConnect remote desktop access product and urges customers to install the patches asap. ConnectWise warns of the following two critic ...
Law enforcement provided additional details about the international Operation Cronos that led to the disruption of the Lockbit ransomware operation. Yesterday, a joint law enforcement action, code ...
The Cactus ransomware gang claims the theft of 1.5TB of data from the Energy management and industrial automation firm Schneider Electric. The Cactus ransomware group claims responsibility for pil ...
An international law enforcement operation codenamed 'Operation Cronos' led to the disruption of the LockBit ransomware operation. A joint law enforcement action, code-named Operation Cronos, con ...
The Raccoon Infostealer operator, Mark Sokolovsky, was extradited to the US from the Netherlands to appear in a US court. In October 2020, the US Justice Department charged a Ukrainian national, M ...
An APT group, tracked as TAG-70, linked to Belarus and Russia exploited XSS flaws in Roundcube webmail servers to target over 80 organizations. Researchers from Recorded Future’s Insikt Group id ...
Resecurity has identified an increasing trend of cryptocurrency counterfeiting, the experts found several tokens impersonating major brands, government organizations and national fiat currencies. ...
SolarWinds addressed three critical vulnerabilities in its Access Rights Manager (ARM) solution, including two RCE bugs. SolarWinds has fixed several Remote Code Execution (RCE) vulnerabilities in ...
Cybersecurity firm ESET has addressed a high-severity elevation of privilege vulnerability in its Windows security solution. ESET addressed a high-severity vulnerability, tracked as CVE-2024-0353 ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
A Ukrainian national pleaded guilty to his role in the Zeus and IcedID operations, which caused tens of millions of dollars in losses. Ukrainian national Vyacheslav Igorevich Penchukov has pleaded ...
CISA warns that the Akira Ransomware gang is exploiting the Cisco ASA/FTD vulnerability CVE-2020-3259 (CVSS score: 7.5) in attacks in the wild. This week the U.S. Cybersecurity and Infrastructure ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Microsoft Exchange and Cisco ASA and FTD bugs to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastru ...
The U.S. government offers rewards of up to $10 million for information that could lead to the identification or location of ALPHV/Blackcat ransomware gang leaders. The U.S. Department of State is ...
U.S. CISA revealed that threat actors breached an unnamed state government organization via an administrator account belonging to a former employee. The U.S. Cybersecurity and Infrastructure Secur ...
Russia-linked APT group Turla has been spotted targeting Polish non-governmental organizations (NGO) with a new backdoor dubbed TinyTurla-NG. Russia-linked cyberespionage group Turla has been spo ...
The US authorities dismantled the Moobot botnet, which was controlled by the Russia-linked cyberespionage group APT28. A court order allowed US authorities to neutralize the Moobot botnet, a netwo ...
On February 12, 2023, a cyber attack halted operations at five production plants of German battery manufacturer Varta. On February 13, German battery manufacturer Varta announced that a cyber atta ...
The office of South Korean President Yoon Suk Yeol said that North Korea-linked actors breached the personal emails of one of his staff members. The office of South Korean President Yoon Suk Yeol ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds 2 Microsoft Windows flaws to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agenc ...
Microsoft and OpenAI warn that nation-state actors are using ChatGPT to automate some phases of their attack chains, including target reconnaissance and social engineering attacks. Multiple nation ...
Researchers reported that attackers can exploit the 'command-not-found' utility to trick users into installing rogue packages on Ubuntu systems. Cybersecurity researchers from cloud security firm ...
Zoom addressed seven vulnerabilities in its desktop and mobile applications, including a critical flaw (CVE-2024-24691) affecting the Windows software. The popular Video messaging giant Zoom relea ...
Adobe Patch Tuesday security updates for February 2024 addressed more than 30 vulnerabilities in multiple products, including critical issues. Adobe Patch Tuesday security updates released by Adob ...
Microsoft Patch Tuesday security updates for February 2024 addressed 72 flaws, two of which are actively exploited in the wild. Microsoft Patch Tuesday security updates for February 2024 resolved ...
Authorities in Romania reported that at least 100 hospitals went offline after a ransomware attack hit the Hipocrate platform. Authorities in Romania confirmed that a ransomware attack that target ...
Bank of America revealed that the personal information of some customers was stolen in a data breach affecting a third-party services provider. Bank of America began notifying some customers follo ...
Maintainers behind the Ransomfeed platform have released Q3 Report 2023 including activities of 185 criminal groups operating worldwide. A comprehensive report delving into the intricate landscape ...
Resecurity has identified a growing trend of malicious cyber-activity targeting sovereign elections globally With more voters than ever in history heading to the polls in 2024, Resecurity has iden ...
Researchers discovered a vulnerability in the code of the Rhysida ransomware that allowed them to develop a decryption tool. Cybersecurity researchers from Kookmin University and the Korea Interne ...
Residential Proxies vs. Datacenter Proxies: this blog post examines the contours of each type and provides info on how to choose the perfect proxy option In the robust landscape of the digital era ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Roundcube Webmail Persistent Cross-Site Scripting (XSS) Vulnerability to its Known Exploited Vulnerabilities catalog. The U.S. Cyb ...
The Canadian government is going to ban the tool Flipper Zero because it is abused by crooks to steal vehicles in the country. The Canadian government announced that it plans to ban the tool Flipp ...
Exploring the Risks: Unveiling 9 Potential Techniques Hackers Employ to Exploit Public Wi-Fi and Compromise Your Sensitive Data We've all used public Wi-Fi: it's convenient, saves our data, and sp ...
The U.S. Justice Department (DoJ) seized the infrastructure that was used to sell the remote access trojan (RAT) Warzone RAT. The Justice Department announced the seizure of internet domains used ...
Raspberry Robin continues to evolve, it was spotted using two new one-day exploits for vulnerabilities either Discord to host samples. Raspberry Robin is a Windows worm discovered by cybers ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Fortinet FortiOS bug to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CI ...
Bitdefender Researchers linked a new macOS backdoor, named RustDoor, to the Black Basta and Alphv/BlackCat ransomware operations. Researchers from Bitdefender discovered a new macOS backdoor, dubb ...
Researcher demonstrated how to exploit a signed Minifilter Driver in a BYOVD attack to terminate a specific process from the kernel. Exploiting a signed Minifilter Driver that can be used to used ...
Black Basta ransomware gang claims the hack of the car maker Hyundai Motor Europe and the theft of three terabytes of their data. BleepingComputer reported that the Car maker Hyundai Motor Europe ...
Fortinet warns that the recently discovered critical remote code execution flaw in FortiOS SSL VPN, tracked CVE-2024-21762, is being actively exploited. Fortinet is warning that the recently disc ...
Ivanti warns customers of a new authentication bypass vulnerability in its Connect Secure, Policy Secure, and ZTA gateway devices. Ivanti has warned customers of a new high-severity security vulne ...
26 key cyber security stats for 2024 that every user should know, from rising cyber crime rates to the impact of AI technology. Cyber Crime Surge: During COVID-19, cyber crimes shot up by 600%, s ...
U.S. Government offers rewards of up to $10 million for information that could help locate, identify, or arrest members of the Hive ransomware group. The US Department of State announced rewards u ...
Several media reported that three million electric toothbrushes were compromised and recruited into a DDoS botnet. Is it true? The Swiss newspaper Aargauer Zeitung first published the news of a DD ...
China-linked APT Volt Typhoon infiltrated a critical infrastructure network in the US and remained undetected for at least five years. US CISA, the NSA, the FBI, along with partner Five Eyes agenc ...
CISCO fixed two critical flaws in Expressway Series collaboration gateways exposing vulnerable devices to cross-site request forgery (CSRF) attacks. Cisco addressed several vulnerabilities in its ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Google Chromium V8 Type Confusion bug to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Se ...
Fortinet warns of two critical OS command injection vulnerabilities in FortiSIEM that could allow remote attackers to execute arbitrary code Cybersecurity vendor Fortinet warned of two critical vu ...
A new vulnerability in JetBrains TeamCity On-Premises can be exploited by threat actors to take over vulnerable instances. JetBrains addressed a critical security vulnerability, tracked as CVE-202 ...
The maintainers of Shim addressed six vulnerabilities, including a critical flaw that could potentially lead to remote code execution. The maintainers of 'shim' addressed six vulnerabilities with ...
China-linked APT group breached the Dutch Ministry of Defence last year and installed malware on compromised systems. Dutch Military Intelligence and Security Service (MIVD) and the General Int ...
Google's TAG revealed that Commercial spyware vendors (CSV) were behind most of the zero-day vulnerabilities discovered in 2023. The latest report published by Google Threat Analysis Group (TAG), ...
Google released Android ’s February 2024 security patches to address 46 vulnerabilities, including a critical remote code execution issue. Google released Android February 2024 security patches ...
A Belarusian and Cypriot national linked with the cryptocurrency exchange BTC-e is facing charges that can lead maximum penalty of 25 years in prison. Aliaksandr Klimenka, a Belarusian and Cypriot ...
The U.S. government imposes visa restrictions on individuals who are involved in the illegal use of commercial spyware. The U.S. State Department announced it is implementing a new policy to impo ...
Hewlett Packard Enterprise (HPE) is investigating a new data breach after a threat actor claimed to have stolen data on a hacking forum. Hewlett Packard Enterprise (HPE) is investigating a new dat ...
The Ivanti SSRF vulnerability tracked as CVE-2024-21893 is actively exploited in attacks in the wild by multiple threat actors. The Ivanti Server-Side Request Forgery (SSRF) vulnerability, identi ...
Airbus Navblue Flysmart+ Manager allowed attackers to tamper with the engine performance calculations and intercept data. Flysmart+ is a suite of apps for pilot EFBs, helping deliver efficient and ...
Scammers stole HK$200 million (roughly $25,5 million) from a multi-national company using a deepfake conf call to trick an employee into transferring the funds. Scammers successfully stole HK$200 ...
Remote desktop software company AnyDesk announced that threat actors compromised its production environment. Remote desktop software company AnyDesk announced on Friday that threat actors had acce ...
What is Data Security Posture Management (DSPM) and how you can mitigate the risks of data leaks such as the 'Mother of All Breaches' Cybersecurity researchers recently uncovered what is now being ...
The US government issued sanctions against six Iranian government officials linked to cyberattacks against critical infrastructure organizations. The U.S. Treasury Department's Office of Foreign ...
A cyber attack forced Lurie Children's Hospital in Chicago to take IT systems offline with a severe impact on its operations. The Lurie Children's Hospital in Chicago took IT systems offline after ...
Resecurity identified bad actors offering a significant number of AnyDesk customer credentials for sale on the Dark Web. Such information being available for cybercriminals could act as a catalys ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Cleaning products giant Clorox estimates the economic impact of the cyber attack that hit the company in August 2023 at $49 million. The Clorox Company is a multinational consumer goods company th ...
A vulnerability impacting the decentralized social network Mastodon can be exploited by threat actors to impersonate and take over any account. A security flaw, tracked as CVE-2024-23832 (CVSS sco ...
Albania’s Institute of Statistics (INSTAT) announced that it was targeted by a sophisticated cyberattack that affected some of its systems. A sophisticated cyberattack on Wednesday hit Albania� ...
An international law enforcement operation, named Synergia, led to the arrest of 31 individuals involved in ransomware, banking malware, and phishing attacks. Operation Synergia was led by Interpo ...
A former software engineer with the U.S. CIA has been sentenced to 40 years in prison for leaking classified documents. Former CIA employee Joshua Adam Schulte has been sentenced to 40 years in p ...
Cloudflare revealed that a nation-state actor breached its internal Atlassian server, gaining access to the internal wiki and its bug database (Atlassian Jira). The incident took place on Thanksg ...
The Computer Emergency Response Team in Ukraine (CERT-UA) reported that a PurpleFox malware campaign had already infected at least 2,000 computers in the country. The Computer Emergency Response T ...
A US man has been sentenced to federal prison for his role in a fraudulent scheme that resulted in the theft of millions of dollars through SIM swapping. Daniel James Junk (22) of Portland was sen ...
CISA is ordering federal agencies to disconnect Ivanti Connect Secure and Ivanti Policy Secure products within 48 hours. For the first time since its establishment, CISA is ordering federal agenci ...
Mandiant spotted new malware used by a China-linked threat actor UNC5221 targeting Ivanti Connect Secure VPN and Policy Secure devices. Mandiant researchers discovered new malware employed by a Ch ...
German police seized 50,000 Bitcoin from the former operator of the now-defunct piracy website movie2k.to. The police in Saxony, Germany, have seized 50,000 Bitcoin (more than $2.1 billion at the ...
Crooks stole around $112 million worth of Ripple XRP from the crypto wallet of Ripple’s co-founder Chris Larsen. This week, crooks stole around $112 million worth of the Ripple-focused cryptocur ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apple improper authentication bug to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Securi ...
Ivanti warns of two new vulnerabilities in its Connect Secure and Policy Secure products, one of which is actively exploited in the wild. Ivanti is warning of two new high-severity vulnerabilities ...
Threat actors are exploiting recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) VPN devices to deliver KrustyLoader. In early January 2024, software firm Ivanti reported that threat ...
Sensitive data and trading activity of over 300K traders leaked online by international fintech firm Direct Trading Technologies. Direct Trading Technologies, an international fintech company, jeo ...
Qualys researchers discovered a root access flaw, tracked as CVE-2023-6246, in GNU Library C (glibc) affecting multiple Linux distributions. The Qualys Threat Research Unit discovered four securit ...
Italian data protection authority regulator authority Garante said that ChatGPT violated European Union data privacy regulations. The Italian data protection authority regulator authority, known a ...
Data of 750 million Indian mobile subscribers was offered for sale on dark web hacker forums earlier in January. CloudSEK researchers warned that a database containing data of 750 million Indian m ...
Juniper Networks released out-of-band updates to fix high-severity flaws in SRX Series and EX Series that can allow attackers to take over unpatched systems. Juniper Networks has released out-of ...
Hundreds of compromised credentials of customers of RIPE, APNIC, AFRINIC, and LACNIC are available on the dark web, Resecurity warns. Resecurity conducted a thorough scan of the Dark Web and ident ...
Energy management and industrial automation firm Schneider Electric suffered a data breach after a Cactus ransomware attack. Schneider Electric is a multinational company that specializes in energ ...
Researchers discovered that Mercedes-Benz accidentally left a private key online exposing internal data, including the company’s source code. RedHunt Labs researchers discovered that Mercedes-Be ...
A flaw in Microsoft Outlook can be exploited to access NTLM v2 hashed passwords by tricking users into opening a specially crafted file. The vulnerability CVE-2023-35636 impacting Microsoft Outloo ...
The U.S. National Security Agency (NSA) admitted to buying internet browsing records from data brokers to monitor Americans' activity online without a court order. U.S. Senator Ron Wyden, D-Ore., ...
Ukraine's security service (SBU) detained an alleged member of the pro-Russia hacker group "the Cyber Army of Russia." Ukraine's security service, the SBU, announced that it has identified and de ...
Multiple proof-of-concept (PoC) exploits for recently disclosed critical Jenkins vulnerability CVE-2024-23897 have been released. Researchers warn that several proof-of-concept (PoC) exploits targ ...
Medusa ransomware gang claimed responsibility for the attack against the Kansas City Area Transportation Authority (KCATA). On January 23, 2023, the Kansas City Area Transportation Authority (KCAT ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The Main Intelligence Directorate of Ukraine's Ministry of Defense states that pro-Ukraine hackers wiped 2 petabytes of data from a Russian research center. The Main Directorate of Intelligence of ...
Bug bounty hunters earned more than $1.3 million for hacking Teslas, infotainment systems, and electric vehicle chargers at the Pwn2Own Automotive competition. The Zero Day Initiative’s Pwn2Own ...
The Russian national malware developer Vladimir Dunaev was sentenced to more than 5 years in prison for his role in the TrickBot operation. The Russian national Vladimir Dunaev (40) has been sente ...
Microsoft revealed that Russia-linked APT Midnight Blizzard has been targeting organizations worldwide in a cyberespionage campaign. Microsoft announced that the Russia-linked APT Midnight Blizzar ...
Jenkins maintainers addressed several security vulnerabilities, including a critical remote code execution (RCE) flaw. Jenkins is the most popular open source automation server, it is maintai ...
Researchers hacked the Tesla infotainment system and found 24 zero-days on day 2 of Pwn2Own Automotive 2024 hacking competition. White hat hackers from the Synacktiv Team (@Synacktiv) compromised ...
The 2023 RedSense report covers long-term observations we have made regarding intel trends and interconnectivity. These observations were made by analyzing numerous 2023 threat findings and disco ...
Cisco addressed a critical flaw in its Unified Communications and Contact Center Solutions products that could lead to remote code execution. Cisco released security patches to address a critical ...
Hewlett Packard Enterprise (HPE) revealed that Russia-linked APT group Midnight Blizzard gained access to its Microsoft Office 365 email system. Hewlett Packard Enterprise (HPE) revealed that alle ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Atlassian Confluence Data Center and Server Template Injection bug to its Known Exploited Vulnerabilities catalog. The U.S. Cyber ...
Thousands of GitLab servers are vulnerable to zero-click account takeover attacks exploiting the flaw CVE-2023-7028. GitLab has recently released security updates to address two critical vulnerabi ...
Researchers released PoC exploit code for a recently disclosed critical authentication bypass flaw in Fortra's GoAnywhere MFT (Managed File Transfer). Researchers with cybersecurity firm Horizon3' ...
Splunk addressed multiple vulnerabilities in Splunk Enterprise, including a high-severity flaw impacting Windows installs. Splunk addressed multiple vulnerabilities in Splunk Enterprise, including ...
Fortra addressed a new authentication bypass vulnerability impacting GoAnywhere MFT (Managed File Transfer) product. Fortra warns customers of a new authentication bypass vulnerability tracked as� ...
The Australian government announced sanctions for a member of the REvil ransomware group for the Medibank hack that occurred in 2022. The Australian government announced sanctions for Aleksandr Ge ...
Financial services company LoanDepot disclosed a data breach that impacted roughly 16.6 million individuals. LoanDepot is a financial services company that primarily operates as a mortgage lender. ...
The Black Basta ransomware gang claimed to have hacked the UK water utility Southern Water, a major player in the UK water industry. Southern Water is a private utility company responsible for col ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds VMware vCenter Server Out-of-Bounds Write bug to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastr ...
Cybersecurity researcher Bob Dyachenko and CyberNews researchers discovered the largest data leak ever discovered. The supermassive leak contains data from numerous previous breaches, comprising a ...
Apple addressed the first zero-day vulnerability that impacts iPhones, Macs, and Apple TVs. The issue is actively exploited in the wild. Apple released security updates to address a zero-day vulne ...
Adaptive phishing campaigns are emerging as an increasingly sophisticated threat in the cybersecurity landscape. The phenomenon This phenomenon represents an evolution of traditional phishing t ...
Researchers warn of a spike in attacks exploiting a now-patched flaw in Apache ActiveMQ to deliver the Godzilla web shell. Trustwave researchers observed a surge in attacks exploiting a now-patche ...
Resecurity researchers warn of massive leak of stolen Thai personally identifiable information (PII) on the dark web by cybercriminals. Resecurity has detected a noticeable increase in data leaks ...
Researchers warned that pirated applications have been employed to deliver a backdoor to Apple macOS users. Jamf Threat Labs researchers warned that pirated applications have been utilized to dist ...
The LockBit ransomware gang claimed to have hacked Subway, the American multinational fast food restaurant franchise. Subway IP LLC is an American multinational fast-food restauran ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Conor Brian Fitzpatrick, the admin of the BreachForums hacking forum, has been sentenced to 20 years supervised release. Conor Brian Fitzpatrick, the admin of the BreachForums hacking forum, was s ...
American global apparel and footwear company VF Corp revealed that the December data breach impacted 35.5 million customers. VF Corporation is an American global apparel and footwear company ...
China-linked group UNC3886 has been exploiting vCenter Server zero-day vulnerability CVE-2023-34048 since at least late 2021. Mandiant researchers reported that China-linked APT group UNC3886 has ...
Ransomware groups claimed that they successfully targeted 4191 victims in 2023, Cybernews researchers report. According to the Ransomlooker tool, the number of ransomware attack victims increased ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Ivanti EPMM flaw CVE-2023-35082 to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Securit ...
Can quantum computing break cryptography? Can it do it within a person’s lifetime? Will it be a cryptopocalypse, as some experts suggest? Can quantum computing break cryptography? Sure, it can. ...
Kansas State University (K-State) suffered a cybersecurity incident that has disrupted part of its network and services. Kansas State University (K-State) suffered a cybersecurity incident that im ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Chrome and Citrix flaws to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency ...
Google warns that the Russia-linked threat actor COLDRIVER expands its targeting and is developing a custom malware. The ColdRiver APT (aka “Seaborgium“, "Callisto", “Star Blizzard”, “TA ...
Experts found multiple flaws, collectively named PixieFail, in the network protocol stack of an open-source reference implementation of the UEFI. Quarkslab researchers discovered nine vulnerabili ...
Researchers devised a "lightweight method," called iShutdown, to determine whether Apple iOS devices have been infected with spyware. Cybersecurity researchers from Kaspersky have identified a " ...
Switzerland believes that the attack claimed by pro-Russian group NoName that hit the government websites is retaliation for Zelensky’s presence at Davos. Switzerland believes that the cyberatta ...
GitHub rotated some credentials after the discovery of a flaw that allowed access to the environment variables of a production container. After GitHub became aware of a vulnerability through its b ...
U.S. CISA and the FBI warned of AndroxGh0st malware used to create a botnet for victim identification and exploitation in target networks. US CISA and the Federal Bureau of Investigation (FBI) r ...
Citrix fixed two actively exploited zero-day vulnerabilities impacting Netscaler ADC and Gateway appliances. Citrix warns customers to install security updates to address two actively exploited ze ...
Google has addressed the first Chrome zero-day vulnerability of the year that is actively being exploited in the wild. Google has released security updates to address the first Chrome zero-day vul ...
Atlassian warns of a critical remote code execution issue in Confluence Data Center and Confluence Server that impacts older versions. Atlassian warns of a critical remote code execution vulnerabi ...
VMware warns customers of a critical vulnerability impacting its Aria Automation multi-cloud infrastructure automation platform. VMware Aria Automation (formerly vRealize Automation) is a modern c ...
Experts warn that recently disclosed Ivanti Connect Secure VPN and Policy Secure vulnerabilities are massively exploited in the wild. Last week, software firm Ivanti reported that threat actors ar ...
Researchers warn of high-severity vulnerability affecting Bosch BCC100 thermostats. Researchers from Bitdefender discovered a high-severity vulnerability affecting Bosch BCC100 thermostats. The ...
Researchers from Bishop Fox found over 178,000 SonicWall next-generation firewalls (NGFW) publicly exploitable. SonicWall next-generation firewall (NGFW) series 6 and 7 devices are affected by two ...
Threat actors exploit a recent Windows SmartScreen bypass flaw CVE-2023-36025 to deliver the Phemedrone info stealer. Trend Micro researchers uncovered a malware campaign exploiting the vulnerabil ...
Balada Injector malware infected more than 7100 WordPress sites using a vulnerable version of the Popup Builder plugin. In September, Sucuri researchers reported that more than 17,000 WordPress we ...
Researchers devised a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners. Cybersecurity researchers from cyber security firm Aqua have uncovered ...
Apple addressed a recently disclosed Bluetooth keyboard injection vulnerability with the release of Magic Keyboard firmware. Apple released Magic Keyboard Firmware Update 2.0.6 to address a recen ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
GitLab addressed two critical flaws impacting both the Community and Enterprise Edition, including a critical zero-click account hijacking vulnerability GitLab has released security updates to add ...
Juniper Networks fixed a critical pre-auth remote code execution (RCE) flaw, tracked as CVE-2024-21591, in its SRX Series firewalls and EX Series switches. Juniper Networks released security updat ...
Investigators from Resecurity’s HUNTER (HUMINT) warn that Indonesia is increasingly being targeted by cyber-threat actors. Investigators from Resecurity’s HUNTER (HUMINT) have found that Indon ...
Researchers published a proof-of-concept (PoC) code for the recently disclosed critical flaw CVE-2023-51467 in the Apache OfBiz. Researchers from cybersecurity firm VulnCheck have created a pro ...
Liquipedia, an online e-sports platform run by Team Liquid, exposed a database revealing its users’ email addresses and other details. Users of the e-sports knowledge base were exposed via a pub ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Ivanti Connect Secure and Microsoft SharePoint bugs to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and In ...
Ivanti revealed that two threat actors are exploiting two zero-day vulnerabilities in its Connect Secure (ICS) and Policy Secure. Software firm Ivanti reported that threat actors are exploiting tw ...
The X account of cybersecurity firm Mandiant was likely hacked through a brute-force password attack, the company revealed. Last week, threat actors hacked the X account of cybersecurity firm Mand ...
Cisco addressed a critical Unity Connection security flaw that can be exploited by an unauthenticated attacker to get root privileges. Cisco has addressed a critical flaw, tracked as CVE-2024-2027 ...
A U.S. District Court sentenced ShinyHunters hacker Sebastien Raoult to three years in prison and ordered him to pay more than $5 million in restitution. The member of the ShinyHunters hacker grou ...
The Healthcare services provider HMG Healthcare has disclosed a data breach that impacted 40 affiliated nursing facilities. In November 2023, the Healthcare services provider HMG Healthcare discov ...
Threat actors hacked the X account of the US Securities and Exchange Commission (SEC) and used it to publish the fake news on the Bitcoin ETF approval. Hackers hijacked the X account of the US Sec ...
Researchers and the Dutch Police released a decryptor for the Tortilla variant of the Babuk ransomware after the arrest of its operator. Cisco Talos researchers obtained a decryptor for the Babuk ...
Microsoft Patch Tuesday security updates for January 2024 addressed a total of 49 flaws, including two critical vulnerabilities. Microsoft Patch Tuesday security updates for January 2024 fixed 49 ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Apache Superset vulnerability to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Secur ...
A hacker group that calls itself Anonymous Arabic is distributing a stealthy remote access trojan called Silver RAT. Cyfirma researchers observed threat actors called ‘Anonymous Arabic’ distr ...
Documents belonging to the Swiss Air Force were leaked on the dark web as a result of cyberattack on a US security provider. Documents belonging to the Swiss Air Force were leaked on the dark web ...
19 individuals worldwide were charged in a transnational cybercrime investigation of the now defunct xDedic marketplace. The U.S. DoJ charged 19 individuals worldwide for their role in the operati ...
A new variant of the Bandook remote access trojan (RAT) was spotted in attacks aimed at Windows machines. Reseachers from Fortinet observed a new variant of a remote access trojan dubbed Bandook� ...
A cyber attack hit the Beirut International Airport, Rafic Hariri (Lebanon), threat actors breached the Flight Information Display System (FIDS). Threat actors hit the Beirut International Airport ...
Bit24.cash has inadvertently exposed sensitive data belonging to nearly 230,000 users, as revealed by Cybernews research. Due to its limited access to foreign financial markets, Iran has embraced ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Sea Turtle cyber espionage group targeted telco, media, ISPs, IT service providers, and Kurdish websites in the Netherlands. Researchers from Dutch security firm Hunt & Hackett observed Sea Tu ...
Researchers discovered a macOS backdoor, called SpectralBlur, which shows similarities with a North Korean APT's malware family. Security researcher Greg Lesnewich discovered a backdoor, call ...
Merck has resolved a dispute with insurers regarding a $1.4 billion claim arising from the NotPetya malware incident. Merck and its insurers have agreed with a $1.4 billion claim arising from the ...
A threat actor announced the sale of the source code and a cracked version of the Zeppelin ransomware builder for $500. Researchers from cybersecurity firm KELA reported that a threat actor ann ...
Ukrainian authorities revealed that Russia-linked APT Sandworm had been inside telecom giant Kyivstar at least since May 2023. Russia-linked APT group Sandworm was inside Ukrainian telecoms giant ...
Ivanti fixed a critical vulnerability in its Endpoint Manager (EPM) solution that could lead to remote code execution (RCE) on vulnerable servers Ivanti has released security updates to address a ...
The MyEstatePoint Property Search app leaked data on nearly half a million of its users, exposing their names and plain-text passwords, the Cybernews research team has found. The all-in-one real e ...
An internet outage impacted Orange Spain after a hacker gained access to the company's RIPE account to misconfigure BGP routing. The hacker, who uses the moniker ‘Snow’, gained access to the R ...
Healthcare technology company HealthEC disclosed a data breach that exposed the personal information of 4.5 million Individuals. Healthcare technology company HealthEC (HEC) disclosed a data brea ...
Researchers discovered three malicious packages in the PyPI repository targeting Linux systems with a cryptocurrency miner. Fortinet researchers discovered three malicious packages in the open-sou ...
The X account of cybersecurity giant Mandiant was hacked, attackers used it to impersonate the Phantom crypto wallet and push a cryptocurrency scam. Crooks hacked the X account of cybersecurity fi ...
Crooks created a new tool that uses Artificial Intelligence (AI) for creating fraudulent invoices used for wire fraud and BEC. Resecurity has uncovered a cybercriminal faction known as "GXC Team", ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Google Chrome and Perl library flaws to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Se ...
Sometimes, you can’t even trust links with your own domain. As the Cybernews research team has discovered, some BMW subdomains were vulnerable to redirect vulnerability, enabling attackers to forge ...
Crypto platform Orbit Chain suffered a cyberattack, threat actors have stolen more than $81 million worth of cryptocurrency. Orbit Chain has suffered a security breach that has resulted in the the ...
Ukraine’s SBU revealed that Russia-linked threat actors hacked surveillance cameras to spy on air defense forces and critical infrastructure in Kyiv. Ukraine’s SBU announced they shut down two ...
JinxLoader is a new Go-based loader that was spotted delivering next-stage malware such as Formbook and XLoader. Researchers from Palo Alto Networks and Symantec warned of a new Go-based malware ...
Researchers discovered an SSH vulnerability, called Terrapin, that could allow an attacker to downgrade the connection's security. Security researchers from Ruhr University Bochum (Fabian Bäumer, ...
Hudson Researchers reported that a mysterious hacker launched a series of attacks against industry-leading companies in Iran. Hudson Researchers reported that on December 20th, a hacker using the ...
These are the Top 2023 Security Affairs cybersecurity stories … enjoy it. CYBERCRIMINALS LAUNCHED “LEAKSMAS” EVENT IN THE DARK WEB EXPOSING MASSIVE VOLUMES OF LEAKED PII AND COMPROMISED DATA ...
CloudSEK researchers analyzed a zero-day exploit that can allow the generation of persistent Google cookies through token manipulation. In October 2023, a developer known as PRISMA first uncovered ...
The Cactus ransomware group claims to have hacked Coop, one of the largest retail and grocery providers in Sweden. Coop is one of the largest retail and grocery providers in Sweden, with approxima ...
Google has agreed to settle a $5 billion privacy lawsuit, which alleged that the company monitored individuals using the Chrome "incognito" mode. Google agreed to settle a $5 billion privacy lawsu ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The INC RANSOM ransomware group claims to have hacked the American multinational corporation Xerox Corp. Xerox Corp provides document management solutions worldwide. The company's Document Technol ...
TuneFab converter, used to convert copyrighted music from streaming platforms such as Spotify, Amazon’s Audible, or Apple Music, has exposed its users' private data. Cybernews research showed th ...
Cyber attacks hit the Assembly of the Republic of Albania and telecom company One Albania, a government agency reported. Albania's National Authority for Electronic Certification and Cyber Securit ...
Ukraine's CERT (CERT-UA) warned of a new phishing campaign by the APT28 group to deploy previously undocumented malware strains. The Computer Emergency Response Team of Ukraine (CERT-UA) warned of ...
An exposed database and secrets on a third-party app puts Clash of Clans players at risk of attacks from threat actors. The Cybernews research team has discovered that the Clash Base Designer Easy ...
The Resecurity's HUNTER unit spotted a new version of the Meduza stealer (version (2.2)) that was released in the dark web. On Christmas Eve, Resecurity's HUNTER unit spotted the author of perspec ...
Experts discovered that Operation Triangulation targeting Apple iOS devices leveraged an undocumented hardware feature. Researchers from the Russian cybersecurity firm Kaspersky discovered that t ...
Leaksmas: On Christmas Eve, multiple threat actors released substantial data leaks, Resecurity experts reported. On Christmas Eve, Resecurity protecting Fortune 100 and government agencies globall ...
A Lockbit ransomware attack against the German hospital network Katholische Hospitalvereinigung Ostwestfalen (KHO) caused service disruptions at three hospitals. German hospital network Katholisch ...
Experts warn of a zero-day flaw that affects Apache OfBiz, an open-source Enterprise Resource Planning (ERP) system. Experts warn of an authentication bypass zero-day flaw that affects Apache OfBi ...
Researchers discovered a new Android malware dubbed Xamalicious that can take full control of the device and perform fraudulent actions. McAfee Mobile Research Team discovered a new Android backdo ...
Security firm Barracuda addressed a new zero-day, affecting its Email Security Gateway (ESG) appliances, that is actively exploited by the China-linked UNC4841 group. On December 21, network and e ...
Governments should recognize electoral processes as critical infrastructure and enact laws to regulate the use of generative Artificial Intelligence. Elections are scheduled in several countries w ...
Researchers warn of attacks against poorly managed Linux SSH servers that mainly aim at installing DDoS bot and CoinMiner. Researchers at AhnLab Security Emergency Response Center (ASEC) are warni ...
St Vincent’s Health Australia, the largest Australian healthcare provider, suffered a data breach after a cyber attack. St Vincent’s Health Australia is the largest non-profit healthcare prov ...
The Rhysida ransomware group claimed to have hacked Abdali Hospital, a multi-specialty hospital located in Jordan. Abdali Hospital is a multi-specialty hospital located in the modern developm ...
Researchers at NCC Group reported that in November they observed the return of the infamous banking malware Carbanak in ransomware attacks. The cybersecurity firm NCC Group reported that in Novemb ...
Cybersecurity company Resecurity has published the 2024 Cyber Threat Landscape Forecast. Resecurity, a Los Angeles-based cybersecurity company protecting Fortune 100 and government agencies worldw ...
The threat actor UAC-0099 is exploiting a flaw in the WinRAR to deliver LONEPAGE malware in attacks against Ukraine. A threat actor, tracked as UAC-0099, continues to target Ukraine. In some att ...
Microsoft reports that the Iran-linked APT33 group is targeting defense contractors worldwide with FalseFont backdoor. Microsoft says the APT33 (aka Peach Sandstorm, Holmium, Elfin, and Magic ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box.Enjoy a new round of the weekly SecurityAf ...
A joint law enforcement operation led by Europol and the ENISA, along with private security firms, identified 443 online shops compromised with digital skimming. Europol and ENISA collaborated in ...
Video game publisher Ubisoft is investigating reports of an alleged data breach after popular researchers shared evidence of the hack. Ubisoft, the popular video game publisher, is examining repor ...
The LockBit ransomware claims to have hacked accountancy firm Xeinadin threatens to leak the alleged stolen data. The LockBit ransomware claims responsibility for hacking the Xeinadin accountancy ...
Mobile virtual network operator Mint Mobile suffered a new data breach, threat actors had access to customers' personal information. Mint Mobile experienced a recent data breach, exposing customer ...
The Akira ransomware group announced it had breached the network of Nissan Australia, the Australian branch of the car maker giant. The Akira ransomware gang claimed to have breached Nissan Austra ...
A member of the Lapsus$ cyber extortion group, Arion Kurtaj, has been sentenced to an indefinite hospital order. The UK Southwark Crown Court has sentenced Arion Kurtaj, a prominent member of the ...
An exposed instance contained information for a customer relationship management (CRM) system that likely belongs to Goyzer, a real estate property management software maker, the Cybernews research t ...
ESET fixes a high-severity flaw in Secure Traffic Scanning Feature that could have been exploited to cause web browsers to trust sites that should not be trusted. ESET has addressed a vulnerabilit ...
Threat actors are exploiting an old Microsoft Office vulnerability, tracked as CVE-2017-11882, to spread the Agent Tesla malware. Threat actors are exploiting an old Microsoft Office vulnerability ...
More than 22,000 users of Blink Mobility should take the necessary steps to protect themselves against the risk of identity theft. The Cybernews research team has discovered that their personal data ...
Google has released emergency updates to address a new actively exploited zero-day vulnerability in the Chrome browser. Google has released emergency updates to address a new zero-day vulnerabili ...
The German police seized the dark web marketplace Kingdom Market as a result of an international law enforcement operation. The Federal Criminal Police Office in Germany (BKA) and the internet-cri ...
An international law enforcement operation, named HAECHI IV, led to the arrest of approximately 3,500 suspects and the seizure of roughly $300 million worth of assets. Interpol this week announced ...
JaskaGO is a new Go-based information stealer malware that targets both Windows and Apple macOS systems, experts warn. Researchers from AT&T Alien Labs uncovered a previously undetected Go-ba ...
By neglecting to set a password, a BMW dealer in India has jeopardized the entire network of car dealerships in the country and put its clients at risk. The Cybernews research team has discovered ...
Comcast’s Xfinity discloses a data breach after a cyber attack hit the company by exploiting the CitrixBleed vulnerability. Comcast's Xfinity is notifying its customers about the compromise of t ...
The Federal Bureau of Investigation (FBI) announced the seizure of the Tor leak site of the AlphV/Blackcat ransomware group. The FBI seized the Tor leak site of the AlphV/Blackcat ransomware ...
Smishing Triad: Researchers warn crooks impersonating UAE Federal Authority for Identity and citizenship ahead of the Holiday Season Resecurity, Inc. (USA) has identified a new fraudulent campaign ...
An alleged Lockbit 3.0 ransomware attack on the Italian cloud service provider Westpole disrupted multiple services of local and government organizations and municipalities. A cyber attack hit on ...
Info stealers, the type of malware with its purpose in the name, can cripple businesses and everyday users alike. So, how do you protect against them? Info stealers, also known as information stea ...
A group of Pro-Israel hacktivists, called Predatory Sparrow, is suspected of having carried out a cyber attack against petrol stations across Iran. A Pro-Israel hacktivist group, called Predatory ...
Experts warn of a new phishing campaign distributing the QakBot malware, months after law enforcement dismantled its infrastructure. In August, the FBI announced that the Qakbot bot ...
A supply chain attack against Crypto hardware wallet maker Ledger resulted in the theft of $600,000 in virtual assets. Threat actors pushed a malicious version of the "@ledgerhq/connect-kit" npm ...
MongoDB on Saturday announced it is investigating a cyberattack that exposed customer account metadata and contact information. MongoDB on Saturday disclosed it is investigating a cyber attack aga ...
The Mirai-based botnet InfectedSlurs was spotted targeting QNAP VioStor NVR (Network Video Recorder) devices. In November, Akamai warned of a new Mirai-based DDoS botnet, named InfectedSlurs, acti ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The Hunters International ransomware gang claims to have hacked the Fred Hutchinson Cancer Center (Fred Hutch). Another healthcare organization suffered a ransomware attack, the Hunters Internatio ...
Experts uncovered a new Go-based multi-platform malware, tracked as NKAbuse, which is the first malware abusing NKN technology. Researchers from Kaspersky’s Global Emergency Response Team (GERT) ...
The Snatch ransomware group announced it had hacked the food giant Kraft Heinz, the company is investigating the claims. Kraft Heinz is an American food company, it is one of the largest food and ...
Security flaws in Netgate pfSense firewall solution can potentially lead to arbitrary code execution on vulnerable devices. pfSense is a popular open-source firewall solution maintained by Netgat ...
Resecurity has uncovered a meaningful link between three major ransomware groups, BianLian, White Rabbit, and Mario Ransomware. Based on a recent Digital Forensics & Incident Response (DFIR) e ...
GokuMarket, a centralized crypto exchange owned by ByteX, left an open instance, revealing the details of virtually all of its users, the Cybernews research team has discovered. The leak comes aft ...
The Idaho National Laboratory (INL) announced that it has suffered a data breach impacting more than 45,000 individuals. In November, the hacktivist group SiegedSec claimed responsibility for the ...
Users of Ubiquiti WiFi products started reporting that they are accessing other people’s devices when logging into their accounts. Some users of Ubiquiti wifi products started reporting unexpec ...
Russia-linked cyber espionage group APT29 has been targeting JetBrains TeamCity servers since September 2023. Experts warn that the Russia-linked APT29 group has been observed targeting JetBrains ...
Microsoft's Digital Crimes Unit seized multiple domains used by cybercrime group Storm-1152 to sell fraudulent Outlook accounts. Microsoft's Digital Crimes Unit seized multiple domains used by a c ...
French police arrested a Russian national who is suspected of laundering money resulting from the criminal activity of the Hive ransomware gang. The French authorities arrested in Paris a Russian ...
Researchers linked a sophisticated botnet, tracked as KV-Botnet, to the operation of the China-linked threat actor Volt Typhoon. The Black Lotus Labs team at Lumen Technologies linked a small offi ...
A Joint Committee on the National Security Strategy (JCNSS) warns of the high risk of a catastrophic ransomware attack on the UK government. The British government is accused of failing to mitigat ...
Microsoft warns that threat actors are using OAuth applications cryptocurrency mining campaigns and phishing attacks. Threat actors are using OAuth applications such as an automation tool in crypt ...
Sophos backports the patch for CVE-2022-3236 for end-of-life (EOL) firewall firmware versions due to ongoing attacks exploiting the issue. Sophos backports the fix for the critical code injection ...
Microsoft Patch Tuesday security updates for December 2023 addressed 33 vulnerabilities in multiple products, including a zero-day. Microsoft Patch Tuesday security updates for December 2023 addre ...
The Ukrainian government's military intelligence service announced the hack of the Russian Federal Taxation Service (FNS). Hackers of the Main Intelligence Directorate of the Ministry of Defense o ...
Kyivstar, the largest Ukraine service provider, was hit by a cyber attack that paralyzed its services. The attack is linked to the ongoing conflict. Kyivstar, the largest Ukraine service provider ...
The Dubai Taxi Company (DTC) app, which provides taxi, limousine, and other transport services, left a database open to the public, exposing sensitive customer and driver data. Dubai Taxi Company, ...
North Korea-linked APT group Lazarus was spotted exploiting Log4j vulnerabilities to deploy previously undocumented remote access trojans. The North Korea-linked APT group Lazarus is behind a ne ...
Apple rolled out emergency security updates to backport patches for two actively exploited zero-day flaws to older devices. The company released iOS 17.2 and iPadOS 17.2 which address a dozen of ...
Toyota Financial Services (TFS) disclosed a data breach, threat actors had access to sensitive personal and financial data. Toyota Financial Services (TFS) is warning customers it has suffered a d ...
The Apache Software Foundation addressed a critical remote code execution vulnerability in the Apache Struts 2 open-source framework. The Apache Software Foundation released security updates to ad ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds two Qlik Sense vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security ...
ENISA has signed a Working Arrangement with the US CISA to enhance capacity-building, best practices exchange and awareness. The European Union Agency for Cybersecurity (ENISA) has signed a Workin ...
Researchers discovered a lock screen bypass bug in Android 14 and 13 that could expose sensitive data in users' Google accounts. The security researcher Jose Rodriguez (@VBarraquito) discovered a ...
WordPress 6.4.2 addressed a security vulnerability that could be chained with another flaw to achieve remote code execution. WordPress released a security update to address a flaw that can be chai ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Threat actors launched a cyberattack on an Irish water utility causing the interruption of the power supply for two days. Threat actors hacked a small water utility in Ireland and interrupted the ...
A set of flaws, collectively called 5Ghoul, in the firmware implementation of 5G mobile network modems from major vendors impacts Android and iOS devices. A team of researchers from the Singapore ...
Kentucky health system Norton Healthcare disclosed a data breach after it was a victim of a ransomware attack in May. Norton Healthcare disclosed a data breach after a ransomware attack that hit t ...
Researchers devised a novel attack vector for process injection, dubbed Pool Party, that evades EDR solutions. Researchers from cybersecurity firm SafeBreach devised a set of process injection tec ...
Anatoly Legkodymov, the founder of the Bitzlato cryptocurrency exchange has pleaded in a money-laundering scheme. Anatoly Legkodymov (41) (aka Anatolii Legkodymov, Gandalf, and Tolik), the Russian ...
An Android app with over 100k Google Play downloads and a 4.5-star average rating has let an open instance go unchecked, leaving sensitive user data up for grabs. The Cybernews team discovered the ...
The UK NCSC and Microsoft warned that Russia-linked threat actor Callisto Group is targeting organizations worldwide. The UK National Cyber Security Centre (NCSC) and Microsoft reported that the R ...
Japanese carmaker Nissan announced it has suffered a cyberattack impacting the internal systems at Nissan Oceania. Nissan Oceania, the regional division of the multinational carmaker, announced it ...
A previously undetected Linux RAT dubbed Krasue has been observed targeting telecom companies in Thailand. Group-IB researchers discovered a previously undetected Linux remote access trojan called ...
Australian Software giant Atlassian addressed four critical Remote Code Execution (RCE) vulnerabilities in its products. Atlassian released security patches to address four critical remote c ...
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds four Qualcomm vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security ...
Researchers devised a new post-exploitation tampering technique to trick users into believing that their iPhone is in Lockdown Mode. Researchers from Jamf Threat Labs devised a new post-exploit ta ...
GST Invoice Billing Inventory, a business accounting app for small and medium businesses with over 1M downloads has left a database open, exposing sensitive personal and corporate data up for grabs. ...
The U.S. CISA warns that threat actors are actively exploiting a critical vulnerability in Adobe ColdFusion to breach government agencies. The U.S. Cybersecurity and Infrastructure Security Agency ...
ENISA published the ENISA Threat Landscape for DoS Attacks report to bring new insights to the DoS threat landscape. Denial-of-Service (DoS) attacks pose a persistent and significant security risk ...
Microsoft warns that the Russia-linked APT28 group is actively exploiting the CVE-2023-23397 Outlook flaw to hijack Microsoft Exchange accounts. Microsoft's Threat Intelligence is warning of Russi ...
Google fixed a critical zero-click RCE vulnerability (CVE-2023-40088) with the release of the December 2023 Android security updates. Google December 2023 Android security updates addressed 85 vul ...
Cybersecurity researchers discovered a new variant of the P2PInfect botnet that targets routers and IoT devices. Researchers at Cado Security Labs discovered a new variant of the P2Pinfect botne ...
Microsoft warns of ongoing malvertising attacks using the DanaBot malware to deploy the CACTUS ransomware. Microsoft uncovered ongoing malvertising attacks using the DanaBot Trojan (Storm-1044) to ...
The LockBit ransomware attack on the Industrial & Commercial Bank of China demonstrates the weakness of global financial system to cyberattacks. The ransomware breach that crippled U.S. Treasu ...
Zyxel addressed tens of vulnerabilities that expose users to cyber attacks, including command injection and authentication bypass. Taiwanese vendor Zyxel addressed tens of vulnerabilities in its f ...
Threat actors are using the Agent Raccoon malware in attacks against organizations in the Middle East, Africa and the U.S. Unit42 researchers uncovered a new backdoor named Agent Raccoon, which is ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
Researchers devised an attack technique that could have been used to trick ChatGPT into disclosing training data. A team of researchers from several universities and Google have demonstrated an at ...
WeMystic, a website on astrology, numerology, tarot, and spiritual orientation, left an open database exposing 34GB of sensitive data about the platforms' users. Telling the future is a tricky bus ...
The popular cybersecurity researcher Patrick Wardle dissected the new macOS ransomware Turtle used to target Apple devices. The popular cyber security researcher Patrick Wardle published a detaile ...
The Black Basta ransomware gang infected over 300 victims accumulating ransom payments exceeding $100 million since early 2022. The Black Basta ransomware group has been active since April 2022, l ...
US CISA added ownCloud and Google Chrome vulnerabilities to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added ownCloud and Googl ...
Apple released emergency security updates to fix two actively exploited zero-day flaws impacting iPhone, iPad, and Mac devices. Apple released emergency security updates to address two zero-day vu ...
A critical vulnerability in Zoom Room allowed threat actors to take over meetings and steal sensitive data. Researchers at AppOms discovered a vulnerability in Zoom Room as part of the HackerOne ...
The Rhysida ransomware group claimed to have hacked King Edward VII’s Hospital in London. King Edward VII's Hospital is a private hospital located on Beaumont Street in the Marylebone district o ...
Google released security updates to address a new actively exploited zero-day vulnerability, tracked as CVE-2023-6345, in the Chrome browser. Google on Wednesday released security updates to addre ...
Cloud identity and access management solutions provider Okta revealed additional threat actor activity linked to the October 2023 breach. Okta provided additional details about the October 20 ...
Thousands of secrets have been left exposed on Docker Hub, a platform where web developers collaborate on their code for web applications. While some are harmless API keys, others could lead to unaut ...
Threat actors started exploiting a critical ownCloud vulnerability (CVE-2023-49103) that can lead to sensitive information disclosure. ownCloud is an open-source software platform designed for fil ...
An international law enforcement operation dismantled the core of a ransomware group operating from Ukraine. A joint law enforcement operation led by Europol and Eurojust, with the support of the ...
The Daixin Team group claims to have hacked the North Texas Municipal Water District (US) and threatened to leak the stolen data. The North Texas Municipal Water District (NTMWD) is a regional wa ...
The US Healthcare provider Ardent Health Services disclosed that it was the victim of a ransomware attack last week. Ardent Health Services is a healthcare company that operates hospitals and othe ...
Ukraine's intelligence service announced the hack of the Russian Federal Air Transport Agency, 'Rosaviatsia.' Ukraine's intelligence service announced they have hacked Russia's Federal Air Transpo ...
Threat actors breached the Municipal Water Authority of Aliquippa in Pennsylvania and took control of a booster station. During the weekend, Iranian threat actors hacked the Municipal Water Author ...
The cyber attack that hit the managed service provider (MSP) CTS potentially impacted hundreds in the United Kingdom. CTS is a trusted provider of IT services to the legal sector in the UK. The co ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The Rhysida ransomware group claimed to have hacked the Chinese state-owned energy conglomerate China Energy Engineering Corporation. The Rhysida ransomware gang added the China Energy Engineering ...
UK and South Korea agencies warn that North Korea-linked APT Lazarus is using a MagicLine4NX zero-day flaw in supply-chain attack The National Cyber Security Centre (NCSC) and Korea's National Int ...
Researchers reported that a Hamas-linked APT group is using a Rust-based SysJoker backdoor against Israeli entities. Check Point researchers observed a Hamas-linked APT group is using the SysJoker ...
Almost a million files with minors' data, including home addresses and photos were left open to anyone on the internet, posing a threat to children. During a recent investigation, the Cybernews re ...
Microsoft announced this week it will pay up to $20,000 for security vulnerabilities in its Defender products. Microsoft launched its new Microsoft Defender Bounty Program with a focus on Defender ...
Researchers warn of publicly exposed Kubernetes configuration secrets that could pose a threat of supply chain attack for organizations. Aqua Nautilus researchers warn of publicly exposed Kubernet ...
North Korea-linked Konni APT group used Russian-language Microsoft Word documents to deliver malware. FortiGuard Labs researchers observed the North Korea-linked Konni APT group using a weaponized ...
Threat actors spread Atomic Stealer (AMOS) macOS information stealer via a bogus web browser update as part of the ClearFake campaign. Atomic Stealer (AMOS) macOS information stealer is now being ...
Healthcare services provider Welltok disclosed a data breach that impacted nearly 8.5 million patients in the U.S. Welltok is a company that specializes in health optimization solutions. It provi ...
North Korea-linked APT group Diamond Sleet is distributing a trojanized version of the CyberLink software in a supply chain attack. Microsoft Threat Intelligence researchers uncovered a supply cha ...
American retailer and distributor of automotive parts and accessories AutoZone discloses a data breach after a MOVEit attack. AutoZone is an American retailer and distributor of automotive parts a ...
Mirai-based botnet InfectedSlurs has been spotted exploiting two zero-day RCE flaws to compromise routers and video recorder (NVR) devices. Akamai warned of a new Mirai-based DDoS botnet, named In ...
The Idaho National Laboratory (INL) disclosed a data breach after the SiegedSec hacktivist group leaked stolen human resources data. SiegedSec hacktivists group claimed responsibility for the hack ...
US CISA adds Looney Tunables Linux flaw to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Looney Tunables Linux ...
Citrix urges admins to kill NetScaler user sessions after patching their appliances against the CVE-2023-4966 Citrix Bleed vulnerability. Citrix is providing additional measures to admins who are ...
The Tor Project removed several relays that were used as part of a cryptocurrency scheme and represented a threat to the users. The Tor Project announced the removal of multiple network relays t ...
Experts warn of a surge in NetSupport RAT attacks against education, government, and business services sectors. The Carbon Black Managed Detection & Response team is warning of a surge in the ...
Organizations need to govern and control the API ecosystem, this governance is the role of API management. Uber uses APIs (Application Programming Interfaces) to connect with third-party services ...
The Canadian government discloses a data breach after threat actors hacked two of its contractors. The Canadian government declared that two of its contractors,Brookfield Global Relocation S ...
The Rhysida ransomware group claimed responsibility for the recent cyberattack on the British Library that has caused a major IT outage. The Rhysida ransomware gang added the British Library to th ...
Russia-linked cyberespionage group APT29 has been observed leveraging the CVE-2023-38831 vulnerability in WinRAR in recent attacks. The Ukrainian National Security and Defense Council (NDSC) repor ...
The DarkCasino APT group leveraged a recently disclosed WinRAR zero-day vulnerability tracked as CVE-2023-38831. Researchers at cybersecurity firm NSFOCUS analyzed DarkCasino attack pattern exploi ...
US teenager Joseph Garrison pleads guilty to carrying out a credential stuffing attack on a betting website. US teenager Joseph Garrison (19) has pleaded guilty to his involvement in a credential ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
8Base ransomware operators were observed using a variant of the Phobos ransomware in a recent wave of attacks. Cisco Talos researchers observed 8Base ransomware operators using a variant of the ...
Russia-linked cyberespionage group Gamaredon has been spotted propagating a worm called LitterDrifter via USB. Check Point researchers observed Russia-linked Gamaredon spreading the worm called ...
OpenAI fired its CEO Sam Altman, and the Chief technology officer Mira Murati appointed interim CEO to lead the company. Sam Altman has been removed as CEO of OpenAI. The company announced that Mi ...
Toyota Financial Services discloses unauthorized activity on systems after the Medusa ransomware gang claimed to have hacked the company. Toyota Financial Services confirmed the discovery of unaut ...
US CISA added three new vulnerabilities (tracked as CVE-2023-36584, CVE-2023-1671, and CVE-2023-2551) to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure ...
Google TAG revealed that threat actors exploited a Zimbra Collaboration Suite zero-day (CVE-2023-37580) to steal emails from governments. Google Threat Analysis Group (TAG) researchers revealed t ...
Vietnam Post Corporation, a Vietnamese government-owned postal service, exposed security logs and employee email addresses to external cyber threats Vietnam Post Corporation, a Vietnamese governme ...
Samsung Electronics disclosed a data breach that exposed customer personal information to an unauthorized individual. Samsung Electronics suffered a data breach that exposed the personal informati ...
The FBI and CISA warn of attacks carried out by the Rhysida ransomware group against organizations across multiple industry sectors. FBI and CISA published a joint Cybersecurity Advisory (CSA) to ...
Enterprise software giant SAP addressed a critical improper access control vulnerability in its Business One product. SAP November 2023 Security Patch Day includes three new and three updated secu ...
The Federal Bureau of Investigation (FBI) dismantled the infrastructure behind the illegal botnet proxy service IPStorm. The IPStorm botnet was first uncovered in May 2019 while targeting Windows ...
Mexican online casino Strendus has exposed sensitive user data, including home addresses and the amounts of money they spent on gambling. Strendus, one of the biggest online casinos in Mexico has ...
VMware disclosed a critical bypass vulnerability in VMware Cloud Director Appliance that can be exploited to bypass login restrictions when authenticating on certain ports. VMware disclosed an aut ...
Danish critical infrastructure was hit by the largest cyber attack on record that hit the country, according to Denmark's SektorCERT. In May, Danish critical infrastructure faced the biggest cyber ...
A cyber attack on the logistics giant DP World caused significant disruptions in the operations of several major Australian ports. A cyberattack hit the international logistics firm DP World Aust ...
Experts warn of an alarming rise in ransomware operations targeting the energy sector, including nuclear facilities and related research entities. Resecurity, Inc. (USA) protecting major Fortune 1 ...
US CISA added four vulnerabilities (tracked as CVE-2023-36844, CVE-2023-36845, CVE-2023-36846, and CVE-2023-36847) in Juniper devices to its Known Exploited Vulnerabilities catalog. The U.S. Cybe ...
The LockBit ransomware group published data allegedly stolen from the aerospace giant Boeing in a recent attack. The Boeing Company, commonly known as Boeing, is one of the world’s largest aeros ...
North Korea-linked APT group Sapphire Sleet set up bogus skills assessment portals in attacks aimed at IT job seekers. The North Korea-linked APT group Sapphire Sleet (aka APT38, BlueNoroff, Cagey ...
The Lorenz extortion group leaked the data stolen from the Texas-based Cogdell Memorial Hospital. In early November, the Cogdell Memorial Hospital (Scurry County Hospital District) announced it w ...
The State of Maine disclosed a data breach that impacted about 1.3 million people after an attack hit its MOVEit file transfer install. The State of Maine was the victim of the large-scale hack ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The Royal Malaysian Police announced the seizure of the notorious BulletProftLink phishing-as-a-service (PhaaS) platform. The Royal Malaysian Police announced to have dismantled the notorious Bu ...
The Serbian citizen Milomir Desnica (33) has pleaded guilty to running the dark web Monopoly drug marketplace. Milomir Desnica, a 33-year-old Serbian citizen, admited to being responsible for oper ...
McLaren Health Care (McLaren) experienced a data breach that compromised the sensitive personal information of approximately 2.2 million individuals. McLaren Health Care (McLaren) disclosed a data ...
After ChatGPT, Anonymous Sudan took down the Cloudflare website with a distributed denial-of-service (DDoS) attack. The hacktivist group Anonymous Sudan claimed responsibility for the massive di ...
The Industrial and Commercial Bank of China (ICBC) suffered a ransomware attack that disrupted trades in the US Treasury market. The Industrial and Commercial Bank of China (ICBC) announced it has ...
Microsoft spotted the exploitation of a SysAid zero-day vulnerability in limited attacks carried out by the Lace Tempest group. Microsoft reported the exploitation of a zero-day vulnerability, tra ...
On-demand moving and delivery platform Dolly.com allegedly paid a ransom but crooks found an excuse not to hold their end of the bargain. Cybercriminals are hardly a trustworthy bunch. Case in poi ...
OpenAI confirmed that the outage suffered by ChatGPT and its API on Wednesday was caused by a distributed denial-of-service (DDoS) attack. OpenAI confirmed earlier today that the outage suffered ...
Mandiant reported that Russia-linked Sandworm APT used a novel OT attack to cause power outages during mass missile strikes on Ukraine. Mandiant researchers reported that Russia-linked APT group S ...
Veeam addressed multiple vulnerabilities in its Veeam ONE IT infrastructure monitoring and analytics platform, including two critical issues. Veeam addressed four vulnerabilities (CVE-2023-38547, ...
Pro-Palestinian hackers group 'Soldiers of Solomon' claims to have hacked one of the largest Israeli flour plants causing severe damage to the operations. The Pro-Palestinian hackers group 'Soldie ...
Iran-linked Agonizing Serpens group has been targeting Israeli organizations with destructive cyber attacks since January. Iran-linked Agonizing Serpens group (aka Agrius, BlackShadow,&n ...
Experts warn threat actors that started exploiting a recent critical flaw CVE-2023-22518 in Confluence Data Center and Confluence Server. Over the weekend threat actors started exploiting a recent ...
Taiwanese vendor QNAP warns of two critical command injection flaws in the QTS operating system and applications on its NAS devices. Taiwanese vendor QNAP Systems addressed two critical command in ...
Google warns of multiple threat actors that are leveraging its Calendar service as a command-and-control (C2) infrastructure. Google warns of multiple threat actors sharing a public proof-of-con ...
Threat actors infected more than 10,000 devices worldwide with the 'PrivateLoader' and 'Amadey' loaders to recruit them into the proxy botnet 'Socks5Systemz.' Bitsight researchers uncovered a pro ...
The Treasury Department sanctioned a Russian woman accused of laundering virtual currency on behalf of cybercriminals. The Department of the Treasury’s Office of Foreign Assets Control (OFAC) on ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
North Korea-linked Lazarus group is using new KandyKorn macOS Malware in attacks against blockchain engineers. North Korea-linked Lazarus APT group were spotted using new KandyKorn macOS malware i ...
Kinsing threat actors are exploiting the recently disclosed Linux privilege escalation flaw Looney Tunables to target cloud environments. Researchers are cloud security firm Aqua have observed th ...
Researchers disclosed four zero-day flaws in Microsoft Exchange that can be remotely exploited to execute arbitrary code or disclose sensitive information on vulnerable installs. Trend Micro's Zer ...
Threat actors who breached the Okta customer support system also gained access to files belonging to 134 customers. Threat actors who breached the Okta customer support system in October gained ac ...
Kaspersky researchers are warning of multiple WhatsApp mods that embed a spyware module dubbed CanesSpy. Kaspersky researchers discovered multiple WhatsApp mods that embed a spyware module du ...
The FSB arrested two Russian hackers who are accused of having helped Ukrainian entities carry out cyberattacks on critical infrastructure targets. The Russian intelligence agency Federal Security ...
Iran-linked cyberespionage group MuddyWater is targeting Israeli entities in a new spear-phishing campaign. Iran-linked APT group MuddyWater (aka SeedWorm, TEMP.Zagros, and&nbs ...
Clop ransomware gang gained access to the email addresses of more than 632K US federal employees at the departments of Defense and Justice. Russian-speaking Clop ransomware group gained access to ...
Okta warns approximately 5,000 employees that their personal information was compromised due to a third-party vendor data breach. Cloud identity and access management solutions provider Okta warns ...
Rapid7 researchers warn of the suspected exploitation of a recently disclosed critical security flaw (CVE-2023-46604) in the Apache ActiveMQ. Cybersecurity researchers at Rapid7 are warning of the ...
Boeing confirmed it is facing a cyber incident that hit its global services division, the company pointed out that flight safety isn’t affected. The Boeing Company, commonly known as Boeing, is ...
Data leaks containing Aadhaar IDs in India were caused by the insecurity of 3rd parties while aggregating such information for KYC. According to Resecurity, a global cybersecurity provider protect ...
Researchers speculate that the recent shutdown of the Mozi botnet was the response of its authors to the pressure from Chinese law enforcement. ESET researchers speculate that the recent shutdown ...
US CISA added two vulnerabilities, tracked as CVE-2023-46747 and CVE-2023-46748, in BIG-IP to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agenc ...
Experts warn that threat actors started exploiting the critical flaw CVE-2023-46747 in F5 BIG-IP installs less than five days after PoC exploit disclosure. F5 this week warned customers about a cr ...
A pro-Hamas hacker group is targeting Israeli entities using a new Linux-based wiper malware dubbed BiBi-Linux Wiper. During a forensics investigation, Security Joes Incident Response team di ...
Last weekend, the British Library suffered a cyberattack that caused a major IT outage, impacting many of its services. The British Library is facing a major outage that impacts the website and ma ...
Atlassian warned of a critical security vulnerability, tracked as CVE-2023-22518, in the Confluence Data Center and Server. Atlassian is warning of a critical security flaw, tracked as CVE-2023-2 ...
World-in-HD (WiHD), a French private video torrent community, left an open instance exposing the emails and passwords of all of its users and administrators. WiHD, a popular torrent tracker specia ...
Researchers publicly released the exploit code for the critical Cisco IOS XE vulnerability tracked as CVE-2023-20198. Researchers from Researchers at Horizon3.ai publicly released the exploit code ...
Canada banned the Chinese messaging app WeChat and Kaspersky antivirus on government mobile devices due to privacy and security risks. The Government of Canada announced a ban on the use of the We ...
A man from Orlando was sentenced to prison for SIM Swapping conspiracy that led to the theft of approximately $1M in cryptocurrency. Jordan Dave Persad (20), from Orlando, Florida, was sentenced t ...
eSentire researchers devised a new attack technique, named Wiki-Slack attack, that can be used to redirect business professionals to malicious websites. eSentire Threat Response Unit (TRU) secur ...
HackerOne announced that it has awarded over $300 million bug hunters as part of its bug bounty programs since the launch of its platform. HackerOne announced that it has surpassed $300 million in ...
A sophisticated malware tracked as StripedFly remained undetected for five years and infected approximately one million devices. Researchers from Kaspersky discovered a sophisticated malware, dubb ...
IT Army of Ukraine hacktivists have temporarily disrupted internet services in some of the territories that have been occupied by Russia. Ukrainian hacktivists belonging to the IT Army of Ukraine� ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The Pwn2Own Toronto 2023 hacking competition is over, bug hunters earned $1,038,500 for 58 zero-day exploits. The Pwn2Own Toronto 2023 hacking competition is over, the organizers awarded $1,038,25 ...
The Lockbit ransomware gang claims to have hacked the aerospace manufacturer and defense contractor Boeing and threatened to leak the stolen data. The Boeing Company, commonly known as Boeing, is ...
France National Agency for the Security of Information Systems warns that the Russia-linked APT28 group has breached several critical networks. The French National Agency for the Security of Infor ...
How residential proxies using real IPs from diverse locations enable businesses to gather comprehensive and accurate data from the web Since the adoption of the first digital tools and connection ...
F5 warns customers of a critical vulnerability impacting BIG-IP that could lead to unauthenticated remote code execution. F5 is warning customers about a critical security vulnerability, tracked a ...
Hello Alfred, an in-home hospitality app, left a database accessible without password protection, exposing almost 170,000 records containing private user data. Hello Alfred is a one-stop applicat ...
Boffins devised a new iLeakage side-channel speculative execution attack exploits Safari to steal sensitive data from Macs, iPhones, and iPads. A team of researchers from the University of Michiga ...
Cloudflare mitigated thousands of hyper-volumetric HTTP distributed denial-of-service (DDoS) attacks exploiting the flaw HTTP/2 Rapid Reset. Cloudflare DDoS threat report of 2023 states that the c ...
Japanese watchmaker Seiko revealed that the attack that suffered earlier this year was carried out by the Black Cat ransomware gang. On August 10, 2023, the Japanese maker of watches Seiko disclos ...
Russia-linked threat actor Winter Vivern has been observed exploiting a zero-day flaw in Roundcube webmail software. Russian APT group Winter Vivern (aka TA473) has been observed exploiting a ze ...
The Pwn2Own Toronto 2023 hacking contest has begun and during the first day, participants received $438,750 in prizes! During the Day 1 of the Pwn2Own Toronto 2023 hacking contest, the organizatio ...
VMware addressed a critical out-of-bounds write vulnerability, tracked as CVE-2023-34048, that impacts vCenter Server. vCenter Server is a critical component in VMware virtualization and cloud c ...
Citrix warned of attacks actively exploiting the vulnerability CVE-2023-4966 in NetScaler ADC and Gateway appliances. Citrix is urging administrators to secure all NetScaler ADC and Gateway applia ...
On September 18th, the Cybernews research team discovered two publicly hosted environment files (.env) attributed to New England Biolabs. Leaving environment files open to the public is one of the ...
A former NSA employee has pleaded guilty to charges of attempting to transmit classified defense information to Russia. Jareh Sebastian Dalke (31), a former NSA employee has admitted to attempting ...
VMware is aware of the availability of a proof-of-concept (PoC) exploit code for an authentication bypass flaw in VMware Aria Operations for Logs. VMware warned customers of the availability of a ...
1Password detected suspicious activity on its Okta instance after the recent compromise of the Okta support system. The password management and security application 1Password announced it had dete ...
Hundreds of millions of PII records belonging to Indian residents, including Aadhaar cards, are being offered for sale on the Dark Web. PII Belonging to Indian Citizens, Including their Aadhaar ID ...
The Spanish police have arrested 34 members of the cybercriminal group that is accused of having stolen data of over four million individuals. The Spanish police have arrested 34 members of a cybe ...
US CISA added the vulnerability CVE-2023-20273 in Cisco IOS XE to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the vulner ...
Cisco found a second IOS XE zero-day vulnerability, tracked as CVE-2023-20273, which is actively exploited in attacks in the wild. Cisco last week warned customers of a zero-day vulnerability, ...
The City of Philadelphia discloses a data breach that resulted from a cyber attack that took place on May 24 and that compromised City email accounts. The City of Philadelphia announced it is inve ...
Researchers discovered three critical remote code execution vulnerabilities in the SolarWinds Access Rights Manager (ARM) product. Security researchers discovered three critical remote code execu ...
The Philippine defense ordered its personnel to stop using AI-based applications to generate personal portraits. The Philippine defense warned of the risks of using AI-based applications to genera ...
Researchers linked Vietnamese threat actors to the string of DarkGate malware attacks on entities in the U.K., the U.S., and India. WithSecure researchers linked the recent attacks using the DarkG ...
MI5 chief warns Chinese cyber espionage reached an epic scale, more than 20,000 people in the UK have now been targeted. The head of MI5, Ken McCallum, warns that Chinese spies targeted more than ...
The International Criminal Court revealed the recent attack was carried out by a threat actor for espionage purposes. The International Criminal Court shared additional information about the cyber ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
A threat actor is selling access to Facebook and Instagram's Police Portal used by law enforcement agencies to request data relating to users under investigation. Cyber security researcher Alon Ga ...
Okta revealed that threat actors breached its support case management system and stole sensitive data that can be used in future attacks. Okta says that threat actors broke into its support case m ...
The U.S. government seized 17 website domains used by North Korean IT workers in a fraudulent scheme to defraud businesses worldwide. The U.S. government announced the seizure of 17 website doma ...
A joint international law enforcement investigation led to the arrest of a malware developer who was involved in the Ragnar Locker ransomware operation. Yesterday we became aware of a joint law en ...
US CISA added the vulnerability CVE-2021-1435 in Cisco IOS XE to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the vulnera ...
More than 40,000 Cisco IOS XE devices have been compromised in attacks exploiting recently disclosed critical vulnerability CVE-2023-20198. Researchers from LeakIX used the indicators of compromis ...
An international law enforcement operation shuts down the infrastructure of the Ragnar Locker ransomware operation. Law enforcement from the US, Europe, Germany, France, Italy, Japan, Spain, Nethe ...
I’m proud to announce the release of the 11th edition of the ENISA Threat Landscape (ETL) on the state of the cybersecurity threat landscape. The Europen Agency for cybersecurity ENISA releases ...
North Korea-linked threat actors are actively exploiting a critical vulnerability CVE-2023-42793 in JetBrains TeamCity. Microsoft warns that North Korea-linked threat actors are actively exploitin ...
Google TAG reported that both Russia and China-linked threat actors are weaponizing the a high-severity vulnerability in WinRAR. Google's Threat Analysis Group (TAG) reported that in recent weeks ...
Hundreds of thousands of clients who opted-in for a screen warranty were exposed when DNA Micro leaked data from its systems. The Cybernews research team found that DNA Micro, a California-based I ...
Experts reported that the vulnerability CVE-2023-4966 in Citrix NetScaler ADC/Gateway devices has been exploited in attacks since late August. On October 10, Citrix published a security bulletin ...
A vulnerability in Synology DiskStation Manager (DSM) could be exploited to decipher an administrator's password. Researchers from Claroty's Team82 discovered a vulnerability, tracked as CVE-2023- ...
Taiwanese manufacturer D-Link confirmed a data breach after a threat actor offered for sale on BreachForums stolen data. The global networking equipment and technology company D-Link confirmed a ...
Threat actors exploited the recently disclosed zero-day flaw (CVE-2023-20198) in a large-scale hacking campaign on Cisco IOS XE devices. Threat actors have exploited the recently disclosed critica ...
Russia-linked APT group Sandworm has hacked eleven telecommunication service providers in Ukraine between May and September 2023. The Russia-linked APT group Sandworm (UAC-0165) has compromised el ...
What is the impact of ransomware on organizations? One employee's mistake can cost a company millions of dollars. Studies show that human error is the root cause of more than 80% of all cyber brea ...
Threat actors are targeting Israeli Android users with a malicious version of the 'RedAlert – Rocket Alerts' that hide spyware. A threat actor is targeting Israeli Android users with a spyware-l ...
Cisco warned customers of a critical zero-day vulnerability in its IOS XE Software that is actively exploited in attacks. Cisco warned customers of a zero-day vulnerability, tracked as CVE-2023-2 ...
Encrypted messaging app Signal denied claims of an alleged zero-day flaw in its platform after a responsible investigation. The popular encrypted messaging app Signal denied claims of an alleged z ...
Microsoft thwarted a large-scale hacking campaign carried out by Akira ransomware operators targeting an unknown industrial organization. Microsoft announced that its Microsoft Defender for Endpo ...
Researchers uncovered an ongoing campaign abusing popular messaging platforms Skype and Teams to distribute the DarkGate malware. From July to September, researchers from Trend Micro observed a ma ...
The Alphv ransomware group added the Morrison Community Hospital to its dark web leak site. Threat actors continue to target hospitals. The ALPHV/BlackCat ransomware group claims to have hacked th ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The Lockbit ransomware gang claims to have hacked the technology services giant CDW and threatens to leak the stolen data. The technology services giant CDW announced it has launched an investiga ...
CISA warns organizations of vulnerabilities and misconfigurations that are known to be exploited in ransomware operations. The US cybersecurity agency CISA is sharing knowledge about vulnerabiliti ...
A cyberespionage campaign, tracked as Stayin' Alive, targeted high-profile government and telecom entities in Asia. Cybersecurity company Check Point uncovered a malicious activity, tracked as ...
FBI and CISA published a joint Cybersecurity Advisory (CSA) to disseminate IOCs, TTPs, and detection methods associated with AvosLocker ransomware. The joint Cybersecurity Advisory (CSA) published ...
In September more than 17,000 WordPress websites have been compromised by the Balada Injector malware. Sucuri researchers reported that more than 17,000 WordPress websites have been compromised i ...
Ransomlooker monitors ransomware groups' extortion sites and delivers consolidated feeds of their claims worldwide. Cybernews presented Ransomlooker, a tool to monitor ransomware groups' extortio ...
This post analyzed the numerous phishing campaigns targeting users and organizations in Italy. Phishing is a ploy to trick users into revealing personal or financial information through an e-mail ...
Researchers observed a new Magecart web skimming campaign changing the websites' default 404 error page to steal credit cards. Researchers from the Akamai Security Intelligence Group unc ...
US CISA added the flaw CVE-2023-21608 in Adobe Acrobat Reader to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added five new fl ...
A Mirai-based DDoS botnet tracked as IZ1H9 has added thirteen new exploits to target routers from different vendors, including D-Link, Zyxel, and TP-Link. Fortinet researchers observed a new Mir ...
Airline Air Europa disclosed a data breach and warned customers to cancel their credit cards after threat actors accessed their card information. Air Europa is a Spanish airline and a subsidiary o ...
Gaza: Resecurity identified threat actors exploiting the conflict to weaponize psychological operations (PSYOPs) campaigns. Amidst the outbreak of war on the Gaza Strip last weekend, Resecurity (L ...
Microsoft Patch Tuesday security updates for October 2023 fixed three actively exploited zero-day vulnerabilities. Microsoft Patch Tuesday security updates for October 2023 addressed a total of 10 ...
A new DDoS technique named 'HTTP/2 Rapid Reset' is actively employed in attacks since August enabling record-breaking attacks. Researchers disclosed a new zero-day DDoS attack technique, named 'HT ...
Many poorly configured security cameras are exposed to hacktivists in Israel and Palestine, placing the owners using them and the people around them at substantial risk. After the Hamas attacks on ...
A vulnerability in the libcue library impacting GNOME Linux systems can be exploited to achieve remote code execution (RCE) on affected hosts. A threat actor can trigger a vulnerability, tracked a ...
Both pro-Israeli and pro-Palestinian hacktivists have joined the fight and are targeting SCADA and ICS systems. Both pro-Israeli and pro-Palestinian hacktivists have joined the fight in the cyber ...
IBM observed a credential harvesting campaign that is targeting Citrix NetScaler gateways affected by the CVE-2023-3519 vulnerability. IBM's X-Force researchers reported that threat actors are con ...
A threat actor has leaked the source code for the first version of the HelloKitty ransomware on a Russian-speaking cybercrime forum. Cybersecurity researchers 3xp0rt reported that a threat actor ...
Microsoft linked a Gaza-based threat actor tracked as Storm-1133 to a series of attacks aimed at private organizations in Israel. The fourth annual Digital Defense Report published by Microsoft l ...
Flagstar Bank announced a data breach suffered by a third-party service provider exposed the personal information of over 800,000 US customers. Flagstar Bank is warning 837,390 US customers that t ...
Researchers warn that more than 70,000 Android smartphones, CTV boxes, and tablets were shipped with backdoored firmware as part of BADBOX network. Cybersecurity researchers at Human Security disc ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
North Korea-linked APT group Lazarus has laundered $900 million worth of cryptocurrency, Elliptic researchers reported. Researchers from blockchain analytics firm Elliptic reported that threat act ...
Threat actors behind the QakBot malware are still active, since August they are carrying out a phishing campaign delivering Ransom Knight ransomware and Remcos RAT. In August, the FBI announced th ...
Hospitality and entertainment company MGM Resorts announced that the costs of the recent ransomware attack costs exceeded $110 million. In September the hospitality and entertainment company MGM R ...
The creation of a dedicated emergency number for cybersecurity could provide an effective solution to this rapidly growing challenge The growing threat of cybercrime is calling for new and innovat ...
Researchers published PoC exploits for CVE-2023-4911 vulnerability (aka Looney Tunables) impacting most popular Linux distributions. The vulnerability CVE-2023-4911 (CVSS score 7.8) is a buffer ov ...
Cisco addressed a critical Static Credentials Vulnerability, tracked as CVE-2023-20101, impacting Emergency Responder. Cisco released security updates to address a critical vulnerability, tracked ...
Belgian intelligence agency State Security Service (VSSE) fears that Chinese giant Alibaba is spying on logistics to gather financial intelligence. The Belgian intelligence service VSSE revealed t ...
The U.S. CISA added JetBrains TeamCity and Windows vulnerabilities to its Known Exploited Vulnerabilities Catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the JetBra ...
NATO is investigating claims that a group called SiegedSec has breached its systems and leaked a cache of unclassified documents online. NATO announced it is investigating claims that a politicall ...
Researcher discovered that global B2B CRM provider Really Simple Systems exposed online a non-password-protected database with million records. Cybersecurity Researcher, Jeremiah Fowler, discovere ...
Sony Interactive Entertainment has notified current and former employees and their family members about a data breach. Sony Interactive Entertainment (SIE) has notified current and former employee ...
Apple released emergency security updates to address a new actively exploited zero-day vulnerability impacting iPhone and iPad devices. Apple released emergency security updates to address a new ...
Atlassian fixed a critical zero-day flaw in its Confluence Data Center and Server software, which has been exploited in the wild. Software giant Atlassian released emergency security updates to ad ...
International mobile virtual network operator Lyca Mobile announced it has been the victim of a cyber attack that disrupted its network. Lyca Mobile is a mobile virtual network operator (MVNO) tha ...
Chipmaker Qualcomm addressed 17 vulnerabilities in various components and warns of three other actively exploited zero-day flaws. Chipmaker Qualcomm released security updates to address 17 vulnera ...
The DRM Report Q2 2023 report provides a detailed insight into the ransomware threat landscape during the period between May and August 2023. In an era where digitalization has woven its web into ...
Threat actors exploited an open redirection vulnerability in the job search platform Indeed to carry out phishing attacks. Researchers from the cybersecurity firm Menlo Security reported that thre ...
A misconfiguration in the Metropolitan Transportation Commission (MTC) systems caused a leak of over 26K files, exposing clients’ parking permits and home addresses. The MTC is a governmental ag ...
Cybersecurity researchers spotted a new malware-as-a-service (MaaS) called BunnyLoader that's appeared in the threat landscape. Zscaler ThreatLabz researchers discovered a new malware-as-a-servi ...
Researchers have identified the exfiltration infrastructure of a LockBit affiliate while investigating a LockBit extortion incident that occurred in Q3 2023. Executive Summary We investigated ...
Researchers from cybersecurity firm TG Soft are warning Italian entities and companies of LockBit 3.0 Black and BlackCat/AlphV attacks. In the last few weeks, two cybercriminal groups th ...
The European Telecommunications Standards Institute (ETSI) disclosed a data breach, threat actors had access to a database of its users. Threat actors stole a database containing the list of users ...
Experts warn of threat actors actively exploiting CVE-2023-40044 flaw in recently disclosed flaw in Progress Software’s WS_FTP products. Progress Software recently warned customers to address a ...
The National Logistics Portal (NLP), a newly launched platform to manage all port operations in India, left public access to sensitive data, posing the risk of a potential takeover by threat actors. ...
North Korea-linked APT group Lazarus impersonated Meta's recruiters in an attack against a Spanish company in the Aerospace industry. ESET researchers linked the North Korea-linked Lazarus AP ...
Experts warn that the recent attack on building automation giant Johnson Controls may have exposed data of the Department of Homeland Security (DHS). Johnson Controls International plc is a multin ...
The ALPHV/BlackCat ransomware gang added McLaren Health Care to the list of victims on its Tor leak site. McLaren Health Care is a not-for-profit healthcare system based in Michigan, United States ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The ALPHV/BlackCat ransomware gang added the hotel chain Motel One to the list of victims on its Tor leak site. Motel One is a German hotel chain that offers budget-friendly accommodations primari ...
The U.S. Federal Bureau of Investigation (FBI) warns of dual ransomware attacks aimed at the same victims. The U.S. Federal Bureau of Investigation (FBI) is warning of dual ransomware attacks, a n ...
Progress Software has addressed a critical severity vulnerability in its WS_FTP Server software used by thousands of IT teams worldwide. Progress Software warned customers to address a critical se ...
A child abuse site has been taken down following a request to German law enforcement by Cybernews research team. A hacker collective, who wanted to remain anonymous, has been relentlessly hunting ...
Experts warn of a critical zero-day vulnerability, tracked as CVE-2023-42115, in all versions of Exim mail transfer agent (MTA) software. A critical zero-day vulnerability, tracked as CVE-2023-421 ...
China-linked threat actors stole around 60,000 emails from U.S. State Department after breaching Microsoft's Exchange email platform in May. China-linked hackers who breached Microsoft's email pl ...
The World Baseball Softball Confederation (WBSC) left open a data repository exposing nearly 50,000 files, some of which were highly sensitive, the Cybernews research team has discovered. On June ...
US CISA added the flaw CVE-2018-14667 in Red Hat JBoss RichFaces Framework to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure Security Agency (CISA) added the ...
Cisco released security updates for an actively exploited zero-day flaw (CVE-2023-20109) that resides in the GET VPN feature of IOS and IOS XE software. Cisco warned customers to install security ...
Johnson Controls International suffered a ransomware attack that impacted the operations of the company and its subsidiaries. Johnson Controls International plc is a multinational conglomerate wit ...
Google released security updates to address a new actively exploited zero-day vulnerability, tracked as CVE-2023-5217, in the Chrome browser. Google on Wednesday released security updates to addre ...
A Russian zero-day broker is willing to pay $20 million for zero-day exploits for iPhones and Android mobile devices. The Russian zero-day broker firm Operation Zero is increasing payouts for top- ...
US and Japanese authorities warn that a China-linked APT BlackTech planted backdoor in Cisco router firmware to hack the businesses in both countries. US and Japanese intelligence, law enforcement ...
Google assigned a maximum score to a critical security flaw, tracked as CVE-2023-5129, in the libwebp image library for rendering images in the WebP format. Google assigned a new CVE identifier f ...
DarkBeam left an Elasticsearch and Kibana interface unprotected, exposing records from previously reported and non-reported data breaches. The leaked logins present cybercriminals with almost limi ...
Following the recently announced data leak from Sony, Ransomed.vc group claimed the hack of the Japanese giant NTT Docomo. Following the recently announced data leak from Sony, the notorious ranso ...
Data lineage is the visualization and tracking of data as it moves through various stages of its lifecycle. In an age where data drives decisions and fuels innovation, understanding the journey of ...
Sony launched an investigation into an alleged data breach after the RansomedVC group claimed the hack of the company. Sony announced it is investigating allegations of a data breach after the Ran ...
Researchers discovered that Canadian Flair Airlines left credentials to sensitive databases and email addresses open for at least seven months Canadian Flair Airlines left credentials to sensitive ...
This week the Rhysida ransomware group claimed the hack of the Kuwait Ministry of Finance and added it to its Tor leak site. Last week a ransomware attack hit the Government of Kuwait, the attack ...
The Better Outcomes Registry & Network (BORN), the Ontario birth registry disclosed a data breach affecting some 3.4 million people. The Better Outcomes Registry & Network (BORN) is a prog ...
A new campaign is spreading Xenomorph malware to Android users in the United States, Spain, Portugal, Italy, Canada, and Belgium. Researchers from ThreatFabric uncovered a new campaign spreading ...
Resecurity research found that the 'Smishing Triad' cybercrime group has expanded its phishing campaign into the United Arab Emirates (UAE). Resecurity research recently found that 'Smishing Triad ...
Crooks stole $200 million from Mixin Network, a free, lightning fast and decentralized network for transferring digital assets. Mixin Network, the Hong Kong-based crypto firm behind a free, lightn ...
A phishing campaign targets Ukrainian military entities using drone manuals as lures to deliver the post-exploitation toolkit Merlin. Securonix researchers recently uncovered a phishing campaign u ...
Experts warn of a critical vulnerability in the TeamCity CI/CD server that can be exploited to take over a vulnerable server. JetBrains TeamCity is a popular and highly extensible Continuous Integ ...
A stealthy APT group tracked as Gelsemium was observed targeting a Southeast Asian government between 2022 and 2023. Palo Alto Unit42 researchers an APT group tracked as Gelsemium targeting a Sout ...
A Nigerian national pleaded guilty to wire fraud and money laundering through business email compromise (BEC). The Nigerian national Kosi Goodness Simon-Ebo (29), who is residing in South Africa, ...
A new variant of a banking trojan, called BBTok, targets users of over 40 banks in Latin America, particularly Brazil and Mexico. Check Point researchers warn of a new variant of a banking trojan ...
Researchers discovered a previously undocumented sophisticated backdoor, named Deadglyph, used by the Stealth Falcon group for espionage in the Middle East ESET researchers discovered a very sophi ...
The Alphv ransomware group claims to have hacked Clarion, the global manufacturer of audio and video equipment for cars and other vehicles. The Alphv ransomware group added Clarion, the global ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
U.S. educational nonprofit organization National Student Clearinghouse disclosed a data breach that impacted approximately 900 US schools. The National Student Clearinghouse (NSC) is a nonprofit o ...
The Government of Bermuda believes that the recent cyberattack against its IT infrastructure was launched by Russian threat actors. This week a cyber attack hit the Government of Bermuda causing t ...
Citizen Lab and Google's TAG revealed that the three recently patched Apple zero-days were used to install Cytrox Predator spyware. Researchers from the Citizen Lab and Google's Threat Analysis Gr ...
US CISA added the flaw CVE-2023-41179 in Trend Micro Apex and other security products to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure Security Agency (CISA) a ...
Air Canada, the flag carrier and largest airline of Canada, announced that the personal information of some employees was exposed as a result of a recent cyberattack. Air Canada, the flag carrier ...
A previously undocumented APT dubbed Sandman targets telecommunication service providers in the Middle East, Western Europe, and South Asia. A joint research conducted by SentinelLabs and QGroup G ...
Apple released emergency security updates to address three new actively exploited zero-day vulnerabilities. Apple released emergency security updates to address three new zero-day vulnerabilities ...
The recently discovered Free Download Manager (FDM) supply chain attack, which distributed Linux malware, started back in 2020. The maintainers of Free Download Manager (FDM) confirmed that the re ...
Exail Technologies, a high-tech manufacturer whose clients include the US Coast Guard, exposed sensitive company data that could’ve enabled attackers to access its databases. Exail, a French hig ...
Pro-Russia hacker group NoName is suspected to have launched a cyberattack that caused border checkpoint outages at several Canadian airports. A massive DDoS cyber attack, likely carried out by Pr ...
Researchers discovered multiple vulnerabilities in the Nagios XI network and IT infrastructure monitoring and management solution. Researchers discovered four vulnerabilities (CVE-2023-40931, CVE- ...
Finnish police announced the takedown of the dark web marketplace PIILOPUOTI which focuses on the sale of illegal narcotics. Finnish Customs announced the seizure of the dark web marketplace Piilo ...
A cyberattack hit the International Criminal Court (ICC) disclosed a cyberattack this week, its systems were compromised last week. The International Criminal Court (ICC) announced that threat act ...
GitLab rolled out security patches to address a critical vulnerability, tracked as CVE-2023-5009, that can be exploited to run pipelines as another user. GitLab has released security patches to ad ...
Trend Micro addressed a zero-day code execution vulnerability (CVE-2023-41179) in Apex One that has been actively exploited in the wild. Trend Micro has released security updates to patch an activ ...
ShroudedSnooper threat actors are targeting telecommunication service providers in the Middle East with a backdoor called HTTPSnoop. Cisco Talos researchers recently discovered a new stealthy impl ...
The cyber attack that hit the cleaning products manufacturer Clorox in August is still affecting the supply of the products to customers. The Clorox Company is a multinational consumer goods compa ...
China-linked threat actor Earth Lusca used a new Linux malware dubbed SprySOCKS in a recent cyber espionage campaign. Researchers from Trend Micro, while monitoring the activity of the China-linke ...
Microsoft AI researchers accidentally exposed 38TB of sensitive data via a public GitHub repository since July 2020. Cybersecurity firm Wiz discovered that the Microsoft AI research division accid ...
The head of Germany’s foreign intelligence service warns of state-sponsored attacks aimed at liquefied natural gas (LNG) terminals in the country. Bruno Kahl, the President of the Bundesnachrich ...
Software development company Retool was the victim of a smishing attack that resulted in the compromise of 27 accounts of its cloud customers. Software development company Retool revealed that 27 ...
Researchers from vx-underground reported that FBI hacker 'USDoD' leaked sensitive data from consumer credit reporting agency TransUnion. TransUnion is an American consumer credit reporti ...
The North Korea-linked APT group Lazarus has stolen more than $240 million worth of cryptocurrency since June 2023, researchers warn. According to a report published by blockchain cyber security f ...
Researchers at healthcare technology firm Nuance blame the Clop gang for a series of cyber thefts at major North Carolina hospitals. The Microsoft-owned healthcare technology firm N ...
One of Thailand's major digital financial platforms, CardX, recently disclosed a data leak that affected their customers. According to the statement published on the CardX official website on Sep ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The Irish Data Protection Commission (DPC) fined TikTok €345 million ($368 million) for violating the privacy of children. The Irish Data Protection Commission (DPC) fined TikTok €345 million ...
The Russian national Dariy Pankov, aka dpxaker, has pleaded guilty to conspiracy to commit wire and computer fraud. The Russian national Dariy Pankov (28), aka dpxaker, is the author of the NLBrut ...
Leading Android health apps expose users to avoidable threats like surveillance and identity theft, due to their risky permissions. Cybernews has the story. The Android challenge In the digital ...
Caesars Entertainment announced it has paid a ransom to avoid the leak of customer data stolen in a recent intrusion. Caesars Entertainment is the world's most geographically diversified casino-en ...
Researchers discovered a free download manager site that has been compromised to serve Linux malware to users for more than three years. Researchers from Kaspersky discovered a free download manag ...
LockBit ransomware group breached two hospitals, the Carthage Area Hospital and the Clayton-Hepburn Medical Center in New York. The Lockbit ransomware group claims to have hacked two major hospita ...
UK Greater Manchester Police (GMP) disclosed a data breach, threat actors had access to some of its employees' personal information. UK Greater Manchester Police (GMP) announced that threat actors ...
The iPhone of a prominent Russian journalist, who is at odds with Moscow, was infected with NSO Group's Pegasus spyware. The iPhone of the Russian journalist Galina Timchenko was compromised with ...
Researchers discovered three security flaws in Kubernetes that can lead to remote code execution on Windows endpoints. Akamai researchers recently discovered a high-severity vulnerability in Kub ...
The multinational aerospace corporation Airbus has launched an investigation into the recent leak of information allegedly stolen from the company. The multinational aerospace corporation Airb ...
3AM is a new strain of ransomware that was spotted in a single incident in which the threat actors failed to deploy the LockBit ransomware in the target infrastructure. Symantec’s Threat Hunte ...
A threat actor tracked as Redfly had infected the systems at a national grid located in an unnamed Asian country for six months starting in January. Symantec’s Threat Hunter Team discovered th ...
Mozilla addressed a critical zero-day vulnerability in Firefox and Thunderbird that has been actively exploited in attacks in the wild. Mozilla rolled out security updates to address a critical ze ...
Microsoft September 2023 Patch Tuesday addressed 59 new flaws, including two vulnerabilities under active attack. Microsoft September 2023 Patch Tuesday security updates addressed 59 vulnerabiliti ...
The international non-governmental organization (NGO) Save the Children International was recently hit with a cyberattack. The charity organization Save the Children International revealed that it ...
Software giant Adobe is warning of a critical security vulnerability in the PDF Acrobat and Reader that is actively exploited in the wild. Adobe Patch Tuesday security updates (APSB23-34) addresse ...
A critical vulnerability in GitHub could have exposed more than 4,000 code packages to Repojacking attack. Checkmarx researchers discovered a new vulnerability in GitHub could have exposed over 4, ...
Hospitality and entertainment company MGM Resorts was hit by a cyber attack that shut down its systems at MGM Hotels and Casinos. Hospitality and entertainment company MGM Resorts was the victim o ...
Anonymous Sudan launched a DDoS attack against Telegram after the company suspended the account of the group. The hacker collective Anonymous Sudan (aka Storm-1359) has launched a distributed deni ...
Iran-linked APT group Charming Kitten used a previously undocumented backdoor named Sponsor in attacks against entities in Brazil, Israel, and the U.A.E. ESET researchers observed a series of a ...
Google rolled out emergency security updates to address a new Chrome zero-day (CVE-2023-4863) actively exploited in the wild. Google rolled out emergency security updates to address a zero-day vul ...
U.S. CISA adds vulnerabilities in Apple devices exploited to install NSO Group's Pegasus spyware on iPhones to Known Exploited Vulnerabilities Catalog US Cybersecurity and Infrastructure Security ...
The U.K. and U.S. governments sanctioned 11 more individuals who were alleged members of the Russia-based TrickBot cybercrime gang. The United States, in coordination with the United Kingdom, sanc ...
Zscaler ThreatLabz detailed a new malware loader, named HijackLoader, which has grown in popularity over the past few months HijackLoader is a loader that is gaining popularity among the cybercrim ...
CyberNews researchers discovered that many universities worldwide are leaking sensitive information and are even open to full takeover. Many universities worldwide, including some of the most pres ...
Evil Telegram: a Trojanized version of the Telegram app was spotted on the Google Play Store, Kaspersky researchers reported. Researchers from Kaspersky discovered several Telegram mods on the Goo ...
Rhysida Ransomware group added three more US hospitals to the list of victims on its Tor leak site after the PROSPECT MEDICAL attack. Recently the Rhysida ransomware group made the headlines becau ...
Akamai announced it has mitigated the largest distributed denial-of-service (DDoS) attack on a U.S. financial company. Cybersecurity firm Akamai successfully identified and prevented a massive d ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
US CISA added critical vulnerability CVE-2023-33246 in Apache RocketMQ to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure Security Agency (CISA) added a critical ...
The Ragnar Locker ransomware gang added Israel's Mayanei Hayeshua hospital to the list of victims on its Tor leak site The Ragnar Locker ransomware gang claimed responsibility for an attack on Isr ...
North Korea-linked threat actors associated with North Korea exploited a zero-day flaw in attacks against cybersecurity experts. North Korea-linked threat actors were observed exploiting a zero-da ...
A zero-day vulnerability (CVE-2023-20269) in Cisco ASA and FTD is actively exploited in ransomware attacks, the company warns. Cisco warns that a zero-day vulnerability (CVE-2023-20269) in Adapti ...
Citizen Lab reported that the actively exploited zero-days fixed by Apple are being used in Pegasus spyware attacks Researchers at Citizen Lab reported that the actively exploited zero-day flaws ( ...
Apple rolled out emergency security updates to address two new actively exploited zero-day vulnerabilities impacting iPhones and Macs. The two Apple zero-day vulnerabilities, tracked as CVE-2023-4 ...
Researchers spotted a new malvertising campaign targeting Mac users with a new version of the macOS stealer Atomic Stealer. Malwarebytes researchers have observed a new malvertising campaign distr ...
A couple of security vulnerabilities in Apache SuperSet could be exploited by an attacker to gain remote code execution on vulnerable systems. Apache Superset is an open-source Data Visualizatio ...
Microsoft revealed that the Chinese group Storm-0558 stole a signing key used to breach government email accounts from a Windows crash dump. In July, Microsoft announced it had mitigated an attack ...
Google released September 2023 Android security updates to address multiple flaws, including an actively exploited zero-day. Google released September 2023 Android security updates that address te ...
Experts warn of an Atlas VPN zero-day flaw impacting the Linux client that can reveal the user's IP address by visiting a website. A Reddit user with the handle 'Educational-Map-8145' published a ...
MITRE and CISA released a Caldera extension for OT that allows the emulation of attacks on operational technology systems. MITRE Caldera is an open-source adversary emulation platform that helps c ...
Three critical remote code execution vulnerabilities in ASUS routers potentially allow attackers to hijack the network devices. ASUS routers RT-AX55, RT-AX56U_V2, and RT-AC86U are affected by thre ...
Crypto gambling site Stake suffered a security breach, and threat actors withdrew $41M of funds stolen including Tether and Ether. Researchers reported abnormally large withdrawals made from the c ...
The nonprofit organization Freecycle Network (Freecycle.org) confirmed that it has suffered a data breach that impacted more than 7 million users. The Freecycle Network (TFN,) is a private, nonpro ...
Meta disrupted two influence campaigns orchestrated by China and Russia, the company blocked thousands of accounts and pages. Meta announced it has taken down two of the largest known covert influ ...
A distributed denial-of-service (DDoS) attack took the site of the German Federal Financial Supervisory Authority (BaFin) down. A distributed denial-of-service (DDoS) attack took the site of the G ...
Resecurity has identified a large-scale smishing campaign, tracked as Smishing Triad, targeting the US Citizens. Earlier episodes have revealed victims from the U.K., Poland, Sweden, Italy, Indon ...
The University of Sydney (USYD) suffered a security breach caused by a third-party service provider that exposed personal information of recent applicants. The University of Sydney (USYD) announce ...
Cybercrime will cost Germany 206 billion euros ($224 billion) in 2023, German digital association Bitkom told Reuters. According to the German digital association Bitkom, cybercrime will have a wo ...
Researcher released PoC exploit code for a recent critical flaw (CVE-2023-34039) in VMware Aria Operations for Networks. At the end of August, VMware released security updates to address two vulne ...
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly Securi ...
The LockBit ransomware gang claims to have breached the Commission des services electriques de Montréal (CSEM). The LockBit ransomware group continues to be one of the most active extortion gangs ...
WannaCry and NotPetya, probably two most damaging cyberattacks in recent history, were both only made possible because of EternalBlue. Here is how the NSA-developed cyber monster works, and how you s ...
Researchers released a free decryptor for the Key Group ransomware that allows victims to recover their data without paying a ransom. Threat intelligence firm EclecticIQ released a free decryption ...
Fashion retailer Forever 21 disclosed a data breach that exposed the personal information of more than 500,000 individuals. On March 20, 2023, the fashion retailer Forever 21 has discovered a cybe ...
Russia-linked threat actors have been targeting Android devices of the Ukrainian military with a new malware dubbed Infamous Chisel. GCHQ’s National Cyber Security Centre and international partn ...
Experts warn of ongoing credential stuffing and brute-force attacks targeting Cisco ASA (Adaptive Security Appliance) SSL VPNs. Cisco is aware of attacks conducted by Akira ransomware threat actor ...
Multinational mass media conglomerate Paramount Global suffered a data breach after an unauthorized party accessed files from certain of its systems. Multinational mass media conglomerate Paramoun ...
The National Safety Council leaked thousands of emails and passwords of their members, including companies such as NASA and Tesla. The National Safety Council has leaked nearly 10,000 emails and p ...
Researchers demonstrated how attackers can abuse the Windows Container Isolation Framework to bypass endpoint security solutions. Researcher Daniel Avinoam at the recent DEF CON hacking conferen ...
VMware fixed two security flaws in Aria Operations for Networks that could be exploited to bypass authentication and gain remote code execution. VMware has released security updates to address two ...
China-linked threat actors breached government organizations worldwide with attacks exploiting Barracuda ESG zero-day. In June, Mandiant researchers linked the threat actor UNC4841 to the attacks ...
Japan’s National Center of Incident Readiness and Strategy for Cybersecurity (NISC) has been infiltrated for months. Threat actors have infiltrated Japan’s National Center of Incident Readines ...
A financially motivated actor linked to the FIN8 group exploits the CVE-2023-3519 RCE in attacks on Citrix NetScaler systems in massive attacks. Sophos X-Ops is tracking an ongoing campaign, which ...
Japan's JPCERT warns of a new recently detected 'MalDoc in PDF' attack that embeds malicious Word files into PDFs. Japan's computer emergency response team (JPCERT) has recently observed a new att ...
A security researcher demonstrated how to discover a target’s IP address by sending a link over the Skype mobile app. The security researcher Yossi discovered that is possible to discover a targ ...
Cisco addressed three high-severity flaws in NX-OS and FXOS software that could cause denial-of-service (DoS) conditions. Cisco this week addressed multiple flaws in its products, including three ...
The cloud and hosting provider Leaseweb suffered a security breach that impacted some "critical" systems of the company. Global hosting and cloud services provider Leaseweb has disabled some "crit ...
Security consulting giant Kroll disclosed a data breach resulting from a SIM-swapping attack against one of its employees. Security consulting firm Kroll revealed that a SIM-swappin ...
China-linked APT group Flax Typhoon targeted dozens of organizations in Taiwan as part of a suspected espionage campaign. Microsoft linked the Chinese APT Flax Typhoon (aka Ethereal Panda) to a cy ...
Proof-of-concept exploit code for critical Ivanti Sentry authentication bypass flaw CVE-2023-38035 has been released. Researchers released a proof-of-concept (PoC) exploit code for critical Ivanti ...
Resecurity researchers identified a zero-day Buffer Overflow vulnerability in the Schneider Electric Accutech Manager product. Resecurity identified a zero-day vulnerability in the Schneider Elec ...