
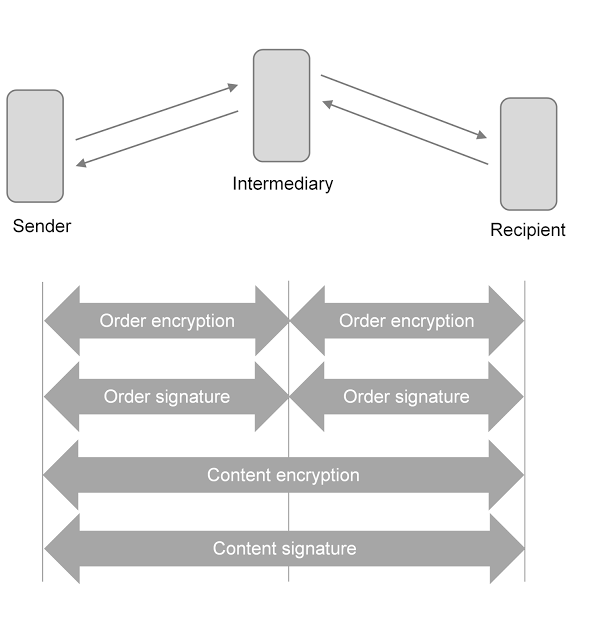
According to the experts at SEC-Consult, the German e-government system OSCI (Online Services Computer Interface) is open to padding oracle attacks and other vulnerabilities due to the use of an insecure communications protocol.
The researchers at SEC Consult found severe vulnerabilities in the OSCI 1.2 Transport library that provides a secure message exchange channel over an untrusted network (i.e. Internet) for German government agencies for eGovernment.
An attacker can exploit the vulnerabilities to decrypt messages, modify signed messages and read arbitrary files from the host that implements the vulnerable OSCI protocol.
“However, SEC Consult found that multiple vulnerabilities allow attackers to decrypt encrypted messages as well as modify signed messages. Moreover, a vulnerability can be used to read arbitrary files from any host that implements the OSCI 1.2 transport protocol using this library.” reads the security advisory.
An External Entity Injection (XXE), tracked as CVE-2017-10670, could be exploited by an attacker to read arbitrary files from the target system, or to trigger a denial-of-service condition on it.
“By sending manipulated XML data to any communication partner, an attacker is able to conduct an XXE attack on the receiving system. This attack allows an attacker to read arbitrary files from the file system of the victim host or to conduct a denial of service attack.” reads the Advisory.
The CVE-2017-10668 vulnerability is linked to the implementation of a number of deprecated encryption algorithms (Triple DES, AES 129, AES 192, and AES 256, all in CBC mode) that open the door to padding oracle attacks.
“Since the supported cipher algorithms do not provide protection against modification (malleability) and the library reveals in an error message whether decryption failed (error code 9202), SEC Consult was able to conduct a padding oracle attack. This attack allows an attacker to bypass transport encryption.” states the advisory.
“In our test setup we were able to decrypt an OSCI processDelivery message on a local machine within half an hour.” states a blog post published by SEC Consult.

A Signature Wrapping attack, tracked as CVE-2017-10669, allows the miscreant to change the contents of a message without invalidating the signature.
“Signature Wrapping attack [CVE-2017-10669] By moving XML elements within the document tree, a signature wrapping attack can be conducted. This allows an attacker to modify the contents of a signed message arbitrarily without invalidating the signature.” states the advisory.
The last issue is a deserialization bug that could be exploited to an external entity injection.
“A class in the library defines the method readObject() that is used by Java to deserialize a stream into an object. This method uses an XML parser to achieve this. However, the XML parser used is configured to resolve external entities. Therefore, an attacker who can influence data that deserialized by an application can conduct an XXE attack 1).”
Experts highlighted that the deserialization bug could be exploited even is the vulnerable application is not using the OSCI-Transport library, it is enough the presence of the OSCI-Transport library in the classpath of an application.
German public agencies should use the latest version of the OSCI-Transport library.
[adrotate banner=”9″]
(Security Affairs – OSCI-Transport library, Germany)
[adrotate banner=”13″]