PoliceOne hacked – Hacker is selling thousands police officials’ accounts
 Pierluigi Paganini
Pierluigi Paganini
 February 04, 2017
February 04, 2017

PoliceOne, a forum used only by only verified law enforcement officials, has been hacked and data dump was offered for sale in a dark web market.
A hacker has stolen over 700,000 user accounts the from a popular law enforcement forum PoliceOne and is offering for sale the entire database.
The PoliceOne forum is used by verified police officers and investigators to exchange information on techniques of investigation, training or other law enforcement centric discussions.
“PoliceOne.com is the #1 resource for up-to-the-minute law enforcement information online. More than 500,000 police professionals nationwide are registered PoliceOne members and trust us to provide them with the most timely, accurate and useful information available anywhere.” reads the description of the website.
The news was reported by Motherboard, the precious data was offered for sale by a hacker that goes online with the moniker of the Berkut.
“We have confirmed the credibility of a purported breach of the PoliceOne forums in 2015 in which hackers were potentially able to obtain usernames, emails and hashed passwords for a portion of our members. While we have not yet verified the claim, we are taking immediate steps to secure user accounts and our forums, which are currently offline while we investigate and gather more information,” a spokesperson for PoliceOne told Motherboard in an email.
“While we store only limited user data and no payment information, we take any breach of data extremely seriously and are working aggressively to resolve the matter. We will be notifying potentially-affected users as a matter of priority and requiring them to change their passwords,” he added.

“Emails from NSA, DHS, FBI and other law enforcement agencies as well as other US government agencies,” Berkut’s listing on the Tochka dark web market reads.
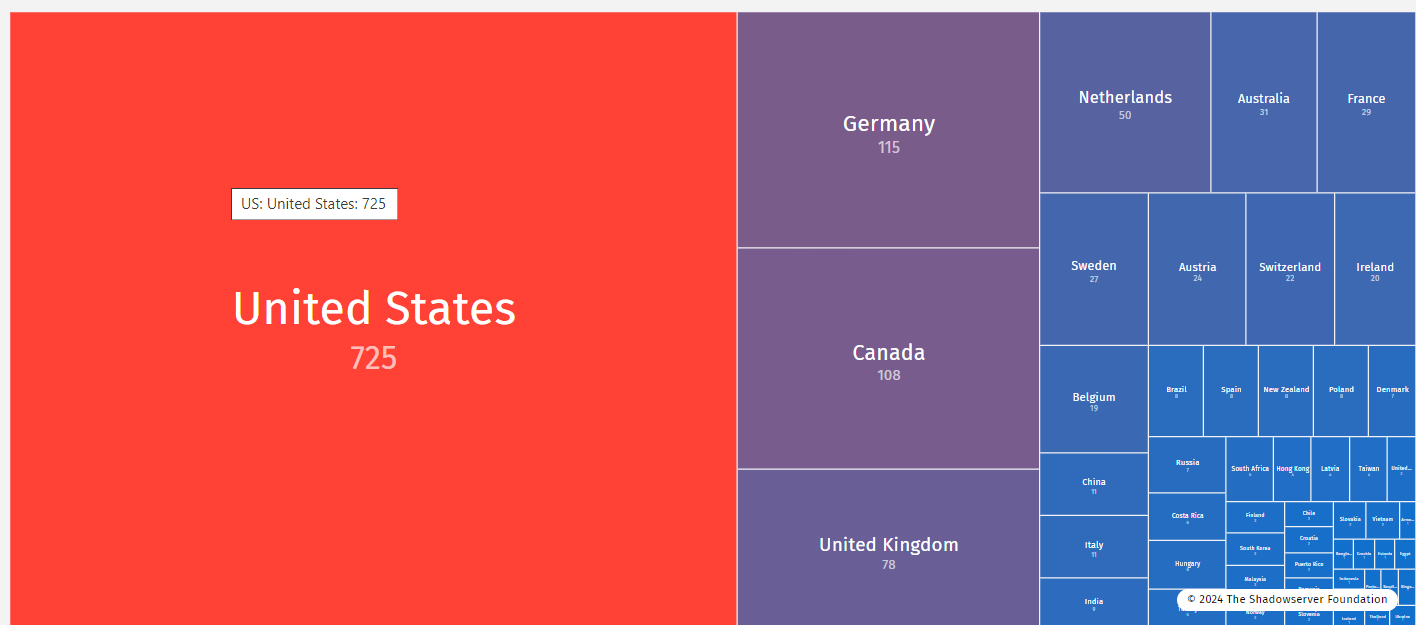
Berkut is selling the full database which includes around 715,000 user accounts and dates from 2015, for $400. He used the Tochka dark web market to sell the data dump that contains emails from the main US intelligence agencies (NSA, DHS, FBI), the hacker also confirmed that he had already sold the archive also on other forums.
Berkut provided Motherboard as proof of the hack several samples of the data, including user details (i.e. usernames, email addresses, subscription dates, MD5 hashed passwords). However, the passwords also included salts—random strings of characters used to make a hash more resilient.
Let me remind you that MD5 hashed passwords are very easy to hack.
“The files did indeed contain valid email addresses from the NSA and other US government agencies; one file allegedly contained over 3,000 account details for Homeland Security staffers.” reported the Motherboard.
“To verify that emails in the dump were connected to real accounts on PoliceOne, Motherboard attempted to create new users with a random selection of email addresses. Out of 15 addresses, 14 were already registered on the site.”
How did Bekrut hack the PoliceOne website?
The PoliceOne was running on a flawed version of the popular vBulletin CMS (likely version 4.2.3), it was quite easy for the hacker to find an exploit online and breach it.
[adrotate banner=”9″]
Pierluigi Paganini
(Security Affairs – vBulletin, data breach)