MalwareMalware is essentially any software that performs actions that are not known and authorized by the user. While most of the malware that we read about in the news or on forums for the most part have damaging effects on the infected device, the term malware also encompasses less damaging software, such as PUPs.Virus
Viruses are a type of malware that require user intervention to infect a device. What this means, is that the victim must actually run the software that contains the virus’ code. Viruses have often been spread via e-mail, i.e. through “chain e-mails” as attachments that are named as something else. Viruses are often spread as files that contain solely malicious code. This means that rather than spreading and masquerading as a legitimate application, viruses are often files that contain nothing but malicious code, which places the burden on the sender to convince their target to download and launch the malicious software.
There are several types of viruses, but one that I will mention are Macro viruses. Macro viruses are spread via Macro code (code that can be embedded inside a Microsoft Office document (e.g. Microsoft Word document, Microsoft Excel spreadsheets) that are launched when the document is opened. There are a very large quantity of Macro viruses still being spread in-the-wild today.
Trojan
Trojans are a type of malware that also require user intervention to infect a device. Like viruses, victims must run the software that contains the Trojan’s code in order for it to successfully compromise the victim’s device. However, Trojans (hence the name “Trojan Horse”) are different from viruses in the sense that they often appear to be a legitimate application that the victim may have been searching for. Often, the malicious code launched by a Trojan is actually appended to the end of a legitimate application to better deceive their targets.
Additionally, there are several types of Trojans. The three that I believe are worth mentioning are:
Trojan Downloader – A Trojan that, when launched, downloads additional file(s) that actually contain the final payload (e.g. ransomware, a DLL containing a backdoor).
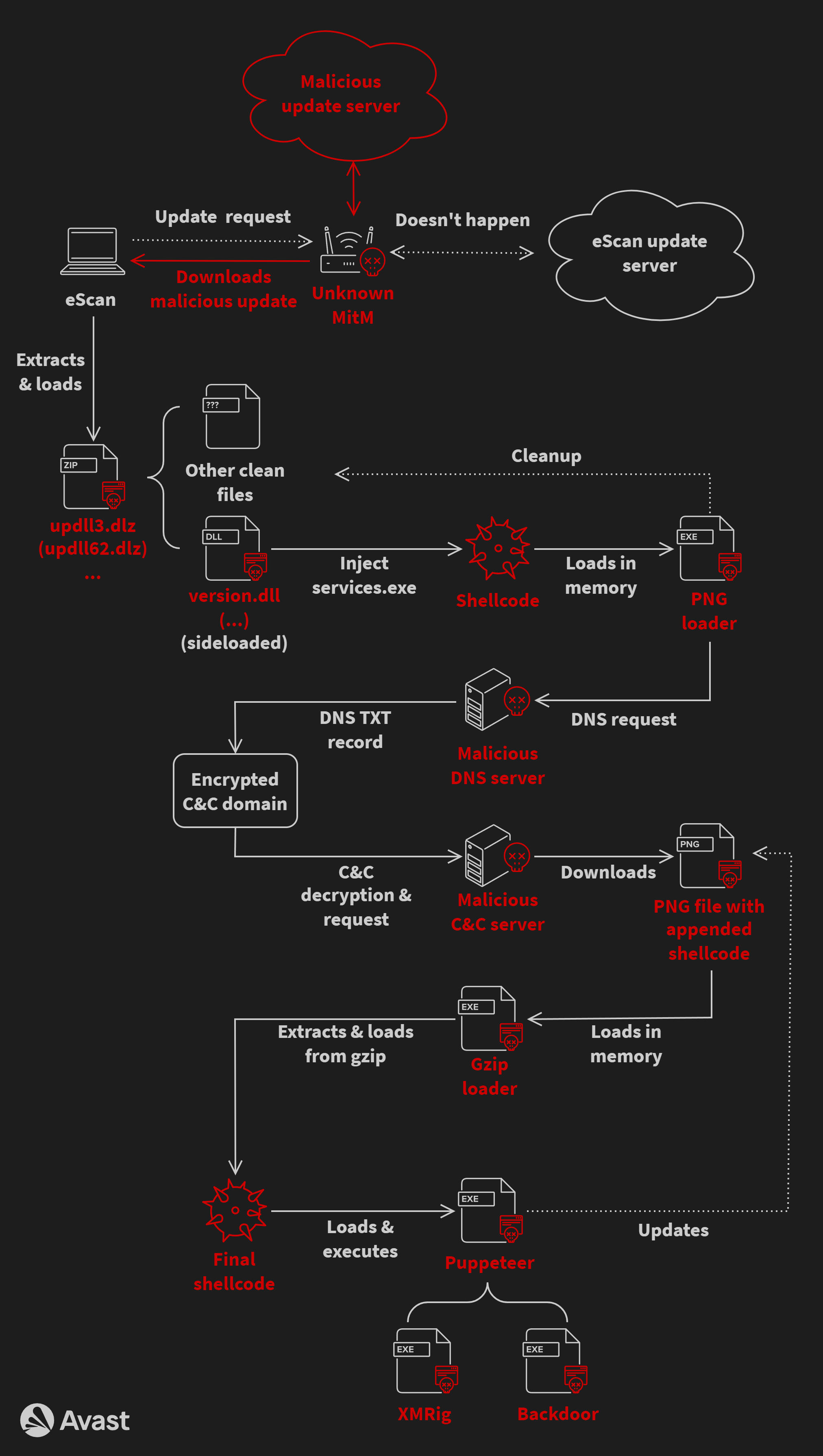
Trojan Injector – A Trojan that, when launched, injects malicious code into another process, often a legitimate process, to evade detection.
Trojan Dropper – A Trojan that, when launched, drops an additional file (usually) containing the malware’s payload. Usually an executable file or DLL containing an additional payload (i.e. the final, most damaging payload) and/or used for persistence (maintaining access to the compromised device).
Worm
Worms are a type of malware that differ from Trojans and Viruses. Worms cause arguably the most damage to the device(s) that they compromise; this is because worms are self-replicating. Worms can spread without user intervention, and in effect, a single worm infection can spread to an entire network. Worms in the news includeStuxnet, Koobface, and Conficker. I set up a vulnerable device and let it run for a couple weeks and logged hundreds of unique Conficker variants within the first week on a brand new device. Worms are still out there, and Conficker is still very active.
Ransomware
Ransomware has been around for quite some time, though it made national headlines a few years ago with the development and spread of CryptoLocker. As can be derived from the name, Ransomware is a type of malware spread by attackers with the goal of demanding a ransom from their victims; most often for financial gain.
Specifically, Crypto Ransomware will go through all of the directories, files and sometimes network shares and mapped drives of the victim’s device. It will open supported files (varies by variant) and then encrypt the contents of each supported file. This renders the files useless, and if the file contains pertinent data and no backup of it exists, this can be quite damaging to an individual or an organization as a whole. Ransomware authors generally demand a ransom payment in order restore affected files to their previous state, usually paid in Bitcoin. However, trusting criminals and funding their activity is never recommended.
Rootkit
Malware that is capable of evading all anti-malware utilities, the affected device’s operating system itself, and that may be extremely hard to remove. Rootkits often infect theMBR of the targeted device, and are distributed by attackers as a “hard-to-detect”, persistent method of accessing their targets. Rootkits often function as keyloggers, and their removal often requires the user to format their device; deleting the infected partition and re-partitioning the device is the most accepted remediation method.
Many people think that system restores are effective methods of restoring a compromised device. For one, they aren’t, but even more so in the case of a rootkit infection. Rootkits are generally installed as drivers; as new restore points are created, older ones are purged, and it’s important to remember that these restore points include copies of drivers and other configuration items. Meaning, eventually, the system restore points will become infected as well.
Keylogger
As the name states, keyloggers record keystrokes on the affected device, usually dumping all logged keystrokes to a file in a discrete location, to later be sent over to the attacker, often via SMTP (e-mail). Keylogging is an easy way for attackers to obtain usernames, passwords, and credit card numbers of their targets.
Remote Access Trojan (RAT)
A type of malware, specifically under the Trojan category, that allows a remote attacker to gain full control of an infected device.
Zombie (or “Bot”)A zombie is a device that has been compromised with malware that listens for commands from a remote attacker (via a command-and-control server), that the remote attacker often has complete control of. Zombies comprise a botnet, and are most often leveraged when carrying out DDoS attacks.Command-and-Control Server (or “C2 Server”)
A command-and-control server (or “C2 Server”) is a server dedicated to managing a botnet (network of zombies). While C2 servers can be dedicated devices set-up and configured by the attacker(s), legitimate websites with known vulnerabilities (commonly: websites running vulnerable versions of WordPress) have often been compromised by attackers and converted into C2 servers. It is not uncommon for an attacker to take control of a vulnerable website and implement the command-and-control functionality in the background, remaining undetected by the actual site owner for quite some time.
Exploit Kit
Many define exploit kits as a type of malware but I disagree. An exploit kit is a full software suite (usually a complete web application written in PHP) that is used to distribute malware in an automated fashion, leveraging exploits to install the malware on vulnerable devices without user intervention (other than browsing a specially crafted page).
Exploit kits serve a landing page that carries out the core functions; this page will scan the target to determine their browser, browser version, installed plug-ins, and other identifying information. Exploit kits have an arsenal of commonly-known vulnerabilities, and sometimes zero-day vulnerabilities. If the target is found to be vulnerable to one of the vulnerabilities in its arsenal, the exploit kit will then leverage the vulnerability to force the download and execution of malware onto the target system.
Zero-Day
A zero-day or zero-day vulnerability is a vulnerability that (was) not previously known to exist by the security community nor the vendor. Attackers exploit these previously unknown vulnerabilities to compromise even the most recently updated, hardened devices. Zero-days are often kept secret for as long as possible by attackers, and are sometimes even sold in “underground” markets.
Obfuscate
Often we see the term "obfuscated" when reading malware analysis reports, but what does this mean? Well, to obfuscate somethinig essentially means to hide something or make something illegible. Malware authors obfuscate their code to render it unreadable and hide its malicious nature; often you will see malicious JavaScripts files to be obfuscated, although in my experience, they’re not quite difficult to deobfuscate.
The obfuscation of code is often done not only to deem it illegible, but different obfuscation methods could lead to different file sizes, giving the file containing the obfuscated a code a different signature, to evade anti-virus detection.
Deobfuscate
Referencing the above definition of obfuscate, to deobfuscate is to do the obfuscate; to take illegible, masked code and turn it into code that can be understood and interpreted. Deobfuscation routines are used to deobfuscate code, and are included with obfuscated code in order to convert the code into a language that can be interpreted by the (host) device.
Packer
Packers are used to obfuscate code, in a sense. Essentially, a malware author will take a malicious binary file (executable, DLL, etc.) and scramble the code around to change the file’s signature, to evade anti-virus detection, increasing the rate of successful infection.
Final Thoughts
About the Author Michael Fratello
Edited by Pierluigi Paganini
(Security Affairs – malware, cybercrime)