The Geopolitical dispute between Russia and Ukraine has its correspondence in the cyberspace, principal security experts have observed an increase in the number of cyber attacks between the two countries. Cyber units on both sides may be actively engaged in online campaigns, in the recent weeks it has been observed the rise of DDoS attacks and cyber attack malware-based, according data provided by security firm FireEye.
Experts at FireEye have collected evidence of the intense activity in the cyberspace between Russia and Ukraine, the analysts have focused the investigation on malware “callbacks”, the communications initiated from an infected PC to the C&C server, over the past 16 months.
“One of the most reliable ways to discover computer network operations is to look for malware “callbacks” – the communications initiated from compromised computers to an attacker’s first-stage command-and-control (C2) server. At FireEye, we detect and analyze millions of such callbacks every year.” “As we track the evolution of callbacks during this period, we see a likely correlation between the overall number of callbacks both to Russia and to Ukraine, and the intensification of the crisis between the two nations,” wrote FireEye senior global threat analyst, Kenneth Geers.
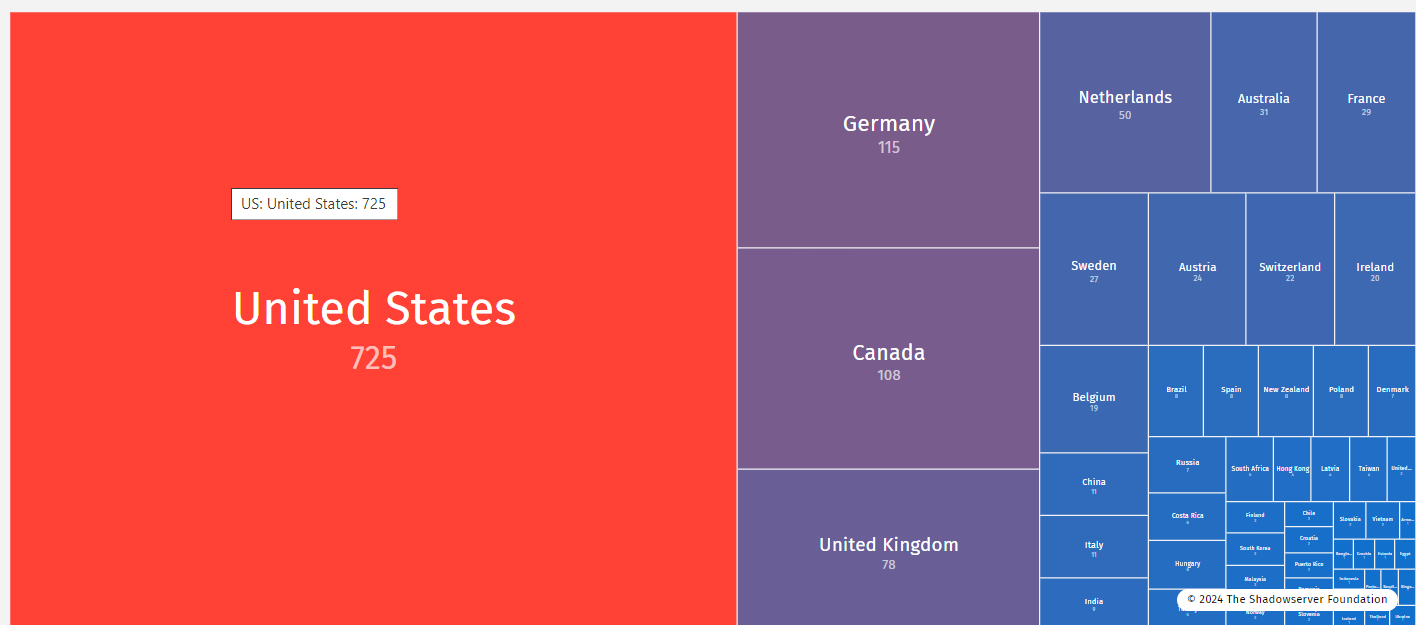
In the following table is proposed the list of nations by number of malware callbacks, concurrently with geopolitical tensions Ukraine has jumped from #12 to #9 Russia is passed from an average #7 to #5.
The greatest jump in the malware callback data occurred in March 2014, exactly in the same period the Russian Government authorized the military force in the Crimea, many experts have found many similarities with tactic adopted by cyber units against Georgia in 2008.
“The rise in callbacks to Russia and Ukraine (or to any other country or region of the world) during high levels of geopolitical tension suggests strongly that computer network operations are being used as one way to gain competitive advantage in the conflict.” states the post.
Below the list of events occurred in March:
- Russia’s parliament authorized the use of military force in Ukraine;
- Vladimir Putin signed a bill incorporating the Crimean peninsula into the Russian Federation;
- The U.S. and EU imposed travel bans and asset freezes on some senior Russian officials;
- Russian military forces massed along the Ukrainian border; and
- Russian energy giant Gazprom threatened to cut off Ukraine’s supply of gas
FireEye observed malicious traffic from any country of the globe, malware callbacks to Russia from compromised computers in a range of countries, including US, Italy, South Korea and Japan.
“It is important to note that nearly half of the world’s countries experienced a decrease in callbacks during this same time frame,” reports the blog post.
Who is behind the cyber operations?
The experts highlighted that it isn’t his intention to suggest that Russia and/or Ukraine are the sole threat actors within the data set proposed and he doesn’t speculate on the precise motives of the attackers behind all of these malware callbacks.
“Within such a large volume of malware activity, there are likely to be lone hackers, ‘patriotic hackers’, cyber criminals, Russian and Ukrainian government operations, and cyber operations initiated by other nations,” Geers said.
Personally, I have no doubts, the rise in malware callbacks in Russia and Ukraine superior to the increment observed in any other area and is for sure related the high level of the geopolitical tension.
The analysis of the cyberspace could provide reliable indicators on political and economical issues in specific countries of the planet, the information collected by FireEye could be integrated for example with data related to the analysis of social media and Tor network use to make a complete picture of the dispute.
This is the new edge of the intelligence.
(Security Affairs – Russia and Ukraine, malware callbacks)