
The ProofPoint security researcher Kafeine discovered a new CryptoMix, CrypMix, variant called CryptoShield 1.0 Ransowmare. Crooks are distributing it via EITest campaign that leverages RIG exploit kit.
“As a note, in this article I will be calling this ransomware CryptoShield as that will most likely be how the victim’s refer to it. It is important to remember, though, that this ransomware is not a brand new infection, but rather a variant of the CryptoMix ransomware family.” reads the article published by Bleepingcomputer.com.
Cyber criminals use to hack websites to distribute the CryptoShield ransomware. EITest is a JavaScript malware that is injected into sites, the malicious code will be executed when victims visit the site.

It downloads the exploit kit from another web site to deliver the CryptoShield ransomware in victim’s computer.

Rig Exploit Kit Traffic – Kafeine credits
When the ransomware is downloaded and executed, it will generate a unique ID for each victim and along with an encryption key. The unique ID and encryption key will be uploaded in the C&C server, then the ransomware encrypts all files with target extensions.
“When CryptoShield encounters a targeted file it will encrypt it using AES-256 encryption, encrypt the filename using ROT-13, and then append the .CRYPTOSHIELD extension to the encrypted file. For example, a file called test.jpg would be encrypted and renamed as grfg.wct.CRYPTOSHIELD In each folder that CryptoShield encrypts a file, it will also create ransom notes named # RESTORING FILES #.HTML and # RESTORING FILES #.TXT.”
Furthermore, the ransomware disables the Windows startup recovery and to clear the Windows Shadow Volume Copies. So, it’s impossible to recover backup files.
“CryptoShield will then display a fake alert stating that there was an application error in Explorer.exe. At first, I was not sure if this was an error produced by the ransomware or just a crashing explorer.exe. As you read the alert closely, though, you can see spelling mistakes such as “momory” and an odd request that you should click on the Yes button in the next Window “for restore work explorer.exe“. The broken English really should have been the giveaway for me.”
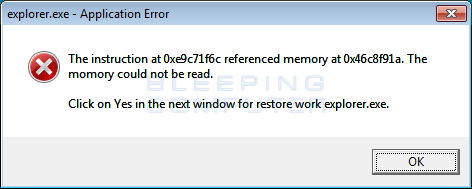
Fake Explorer.exe Alert
“Once you press OK on the above prompt, you will be presented with a User Account Control prompt, which asks if you wish to allow the command “C:\Windows\SysWOW64\wbem\WMIC.exe” process call create “C:\Users\User\SmartScreen.exe” to execute. This explains why the previous alert was being shown; to convince a victim that they should click on the Yes button in the below UAC prompt.”
It is important to keep up to date every program and the OS, exploit kit triggers vulnerabilities in installed software to infect your computer.
The hash for this varian of the ransomware is:
sha256: bb65f0bf3d827958ae447c80ba824e214601094d4dc860b9decc08caae7dd89c
Written by: @GranetMan
 Granet is a young and Junior IT Security Researcher, he is passionate in Linux, Arduino, Digital Forensics, Cyber Security, Free software and Malware Analysis
Granet is a young and Junior IT Security Researcher, he is passionate in Linux, Arduino, Digital Forensics, Cyber Security, Free software and Malware Analysis
| [adrotate banner=”9″] | [adrotate banner=”12″] |
(Security Affairs – CryptoShield, ransomware)
[adrotate banner=”5″]
[adrotate banner=”13″]