
Data-breaches, intellectual property loss and your money… We have all heard the headlines about the social and economic implications of cybercrime, but how bad is the situation really? If we have a serious security problem, how do we get ourselves out of this mess? In particular, what can I do to improve my situation and protect those I care about?
Each week, this easy to understand series of articles quotes cyber security insiders to progressively answer these important questions. In the first week’s article, we learnt that according to the US National Security Agency (NSA): “There is no such thing as ‘secure’ anymore.” Worse, critical aspects of today’s mainstream civilian cyber security ecosystem foundations are fundamentally flawed at the conceptual design, architecture and implementation levels. (See Synaptic Labs’ free 2012 Annual Cyber Security Reports online for the full blow-by-blow disclosure.) In last week’s article, we explored why weak cyber security is one of the most serious (inter)national security challenges we face today. We learnt how computers used in industrial systems can be hacked and reprogrammed to make room sized power generators jump up and down, emit smoke, and shake themselves to pieces. We also learnt how “it is possible to contaminate the database upon which banking operates. [As] there is no gold standard, no dollar bills, so if you can just contaminate the data in one large bank, you could cause global banking to collapse.”
This week we look at the perverse economic incentives driving cybercrime, how we got ourselves into this cyber mess, and explore the concept of due-care.
With our sincerest apologies to Jessie J and her song “Price Tag”, in the cyber espionage and freelancing underground cybercrime communities: “It’s all about the money, money, money. We want your money, money, money. We just want to hack your computer. Forget about your welfare. It’s about your (ha) Cha-Ching Cha-Ching. It’s about your (yeah) Ba-Bling Ba-Bling. Can you feel that (yeah). We’ll pay them with your credit card tonight…”
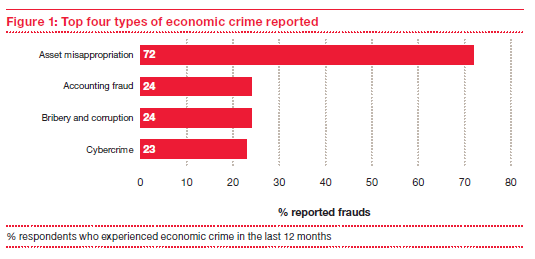
Unfortunately, cyber espionage and cyber crime are profitable industries that are immune to the current economic crisis and their own moral crisis. The survey published by PricewaterhouseCoopers (PwC) paints a dire picture. The PwC “Global Economic Crime Survey” (2011) claims that cybercrime has double-digit growth. Today, cybercrime is the third biggest crime threat to UK businesses, only behind asset theft crimes, fraud and corruption.
Lack of awareness of the cyber threat, tight budgets and contraction of investment in education and prevention, enables criminals to undermine our businesses much more profitably. Brian Snow, former technical director of the US NSA’s Information Assurance Directorate, made the following assessment: (November 2011): “Data-breaches and financial losses are now hurting every segment of the community, it’s a wake up call. They are driving the community to become acutely aware of the (security) weaknesses in current products and systems, and better yet, it forces an increasing awareness of the real need to fix things! The sleeping customer (e.d: citizen) is waking up.”
The groundbreaking study “Norton Cybercrime Report: The Human Impact” (2011) exposes the alarming extent of cybercrime and the feelings of powerlessness and lack of justice felt by its victims worldwide. According to that report, fraud is costing victims more than $388 billion worldwide per annum.
Up to 35 per cent of the global cybercrime bill was paid by US fraud victims, who spent $139 billion on cybercrime last year. Attacks are now occurring at a rate of 141 victims per minute, an alarming statistic. To quote Brian Snow: “No (ed: person or) organization is immune and it is no longer credible to say: Not my problem!”

Unfortunately, it is impossible to effectively manage the cyber threat using a reactive “fire-fighting” approach because many serious attacks have a silent genesis. According to the UK government: “The covert nature of the threat means that the public and businesses can underestimate the risks.” According to Pauline Neville-Jones, former governor and chairman of the British Joint Intelligence Committee and the UK government’s special representative to business on cyber-security says: “There is a vast swathe of corporates who have valuable intellectual property, much more valuable than they understand, which is inadequately protected. They don’t even realise it has been stolen. They don’t even know they have been the subject of attack. They usually have to be told about it by a third party, most of them do not discover it for themselves. The level of awareness is nothing like it needs to be. This is a very, very serious state of affairs.” Sustained attacks can lead to disastrous consequences. Nortel was a victim of Chinese cyber espionage for decades, and recently collapsed in bankruptcy.
We occasionally hear some security experts/vendors pointing the blame at users. Clearly, better training of end-users and business managers would help reduce our collective risk and we applaud the public cyber awareness campaigns in many countries. You can see some very good examples on the ICT Gozo Malta Project website at [ictgozomalta.eu/cyber-security-awareness.html] We should all do what we can to advance our own understanding to protect ourselves and support others!
However we would be dangerously mistaken to place all the blame for our cyber security problems on the user in “main street”. According to Brian Snow, the ICT industry also has a lot to answer for: “There are problems today in Cyber Security practice that impact the community as a whole, and we need to solve those problems soon. They are pervasive, ongoing, and getting worse, not better. Right now, the community at large is applying the wrong or inadequate engineering practices, and taking a lot of short cuts. This adds greatly to our collective security risks.”
In short, no one person, group or sector is to blame. Security short cuts are being taken by all sectors of the global community. To quote Snow: “He who gets to the interface first, wins; so get security and risk experts involved early in your company’s operations and/or designs, indeed, at the very beginning; not as an afterthought!
“If you want transportation in a benign environment, you design a car. If you want transportation in a highly malicious environment, you design a tank! In the current climate on the Internet, I assure you – right now, you need a tank!”
Engendering a life-long ICT learning framework is essential to enabling the growth of the knowledge economy. Cyber security is now seen by the UK government and many other countries as an essential pre-requisite to sustaining that growth. If we want to follow Brian Snow’s guidance and get security in place at the very beginning, we need to integrate cutting-edge cyber security training as a pre-requisite (like reading, writing, arithmetic and IT) for every student in mainstream education systems (see [http://csrc.nist.gov/nice/] for an education framework).
When looking for best practices in managing any serious risks, we can look to the Australian Mining Occupational Health and Safety (OHS) legislation for inspiration. This legislation is generally viewed as being the most progressive (and among the most effective) in the world. It is based upon duty of care, risk management principles and workforce representation, with the primary responsibility for the provision of a safe work place residing with the business operator.
In this framework, government inspectors act as both enforcers of regulations and mentors who encourage good health and safety performance. Enforcement protocols are generally risk-based, with action being defined by both the level and immediacy of the risk.
In this context, “Duty of Care” means that:“
In a cyber security context, the goals are the same: The management of cyber risks and the protection of all stakeholders. This joint duty of cyber care must be shared between governments, vendors, employers and employees. According to Brian Snow: “Each of us has the responsibility:“
Visit [tinyurl.com/cybermalta] for links (hosted on the ICT Gozo Malta website) to some of the best free business cyber security education resources, including free work force training videos. We also strongly recommend you watch Brian Snow’s free 20-minute presentation “Our Cyber Security Status is Grim (and the way ahead will be hard)” for accessible guidance for business people and techies on how to get security right in your organisation. Be sure to read the next article in this series and join us in taking the next steps together to secure (y)our world!
by Ron Kelson, Pierluigi Paganini
References
You can find full citations to all materials referenced in this article, and related cyber security materials including Brian Snow’s presentation, at tinyurl.com/SynapticLabsAnnualReports2012 . Co-author Pierluigi Paganini, Director and CISO of Bit4ID, Italy has 20+ years of security experience and has many years of in-depth investigative cyber security journalism on important cyber events. Find his blog at: securityaffairs.co . ICT Gozo Malta is a joint collaboration between the Gozo Business Chamber and Synaptic Labs, part funded by the Ministry for Gozo, Eco Gozo Project, and a prize winner in the 2012 Malta Government National Enterprise Innovation Awards. www.ictgozomalta.eu has links to free cyber awareness resources for all age groups. To promote Maltese ICT to the world, we encourage all ICT professionals to register on the ICT GM Skills Register and keep aware of developments, both in Cyber Security and other ICT R&D initiatives in Malta and Gozo. For further details contact David Pace at [email protected]