“Then I started using the app on my phone, and monitoring the traffic in the network using WireShark, looking for evidence for unencrypted data that goes through the network or a technique to make this data unencrypted (if it was encrypted). As soon as I logged into my account on my phone, Wireshark has captured unencrypted data that goes through HTTP. This data includes: The pictures that the victims watching, The victim’s session cookies, the victim’s username and ID.” said Mazin.
What do you think about?
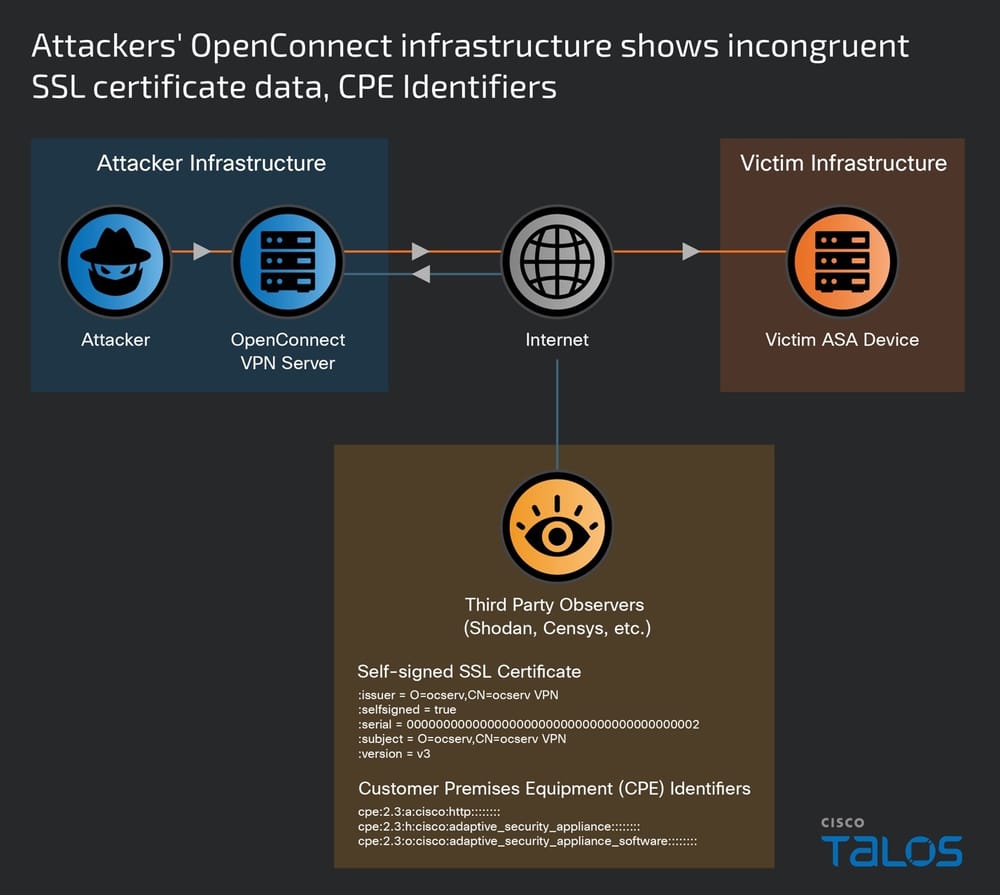
You are right, what Mazin Ahmed is saying is that the Android Instagram app is affected by a session hijacking vulnerability that can be exploited to conduct a man-in-the-middle attack. When the attacker and victims share the same wireless data traffic this kind of attacks is very easy to perform.

Mazen captured the HTTP session cookies and tried to use is from another system/browser… the discovery was disconcerting, he succeeded to hijack the session of the victim’s Instagram account.
“Then, I took the session cookies and used it in my computer, and simply “The Victim’s Session Has Been Hijacked.” he said.
Mazen was surprised that Facebook hasn’t fixed since now a so serious security issue, he immediately reported the flaw to the company which replied that it is aware of the security issue and it is planning to move everything on the Instagram site to HTTPS, but there is no definite date for the change.
“Facebook accepts the risk of parts of Instagram communicating over HTTP not over HTTPS.” replied Facebook.
Security Affairs – (Instagram, hacking)