” We utilized the widely-supported Flash Player plugin to enable socket functionalities not natively present in current browsers, and implemented a partial SSL handshake on our own to capture forged certificates. We deployed this detection mechanism on an Alexa top 10 website, Facebook, which terminates connections through a diverse set of network operators across the world. We analyzed 3;447;719 real-world SSL connections and successfully discovered at least 6;845
(0:2%) of them were forged SSL certificates” report the paper related to the research.
“However, if any antivirus software enabled SSL interception by default, we would expect a higher number of their forged certificates observed. Note that the observed antivirus-related certificatecounts are not representative of the general antivirus usage share of the website’s users, since SSL interception is often an optional feature in these products. However, if any antivirus software enabled SSL interception by default, we would expect a higher number of their forged certificates observed.
Supposing that these users intentionally installed the antivirus software on their hosts, and deliberately turned on SSL scanning, then these antivirus-generated SSL certificates would be less alarming. However, one should be wary of professional attackers that might be capable of stealing the private key of the signing certificate from antivirus vendors, which may essentially allow them to spy on the antivirus’ users (since the antivirus’ root certificate would be trusted by the client). Hypothetically, governments could also compel antivirus vendors to hand over their
signing keys.”
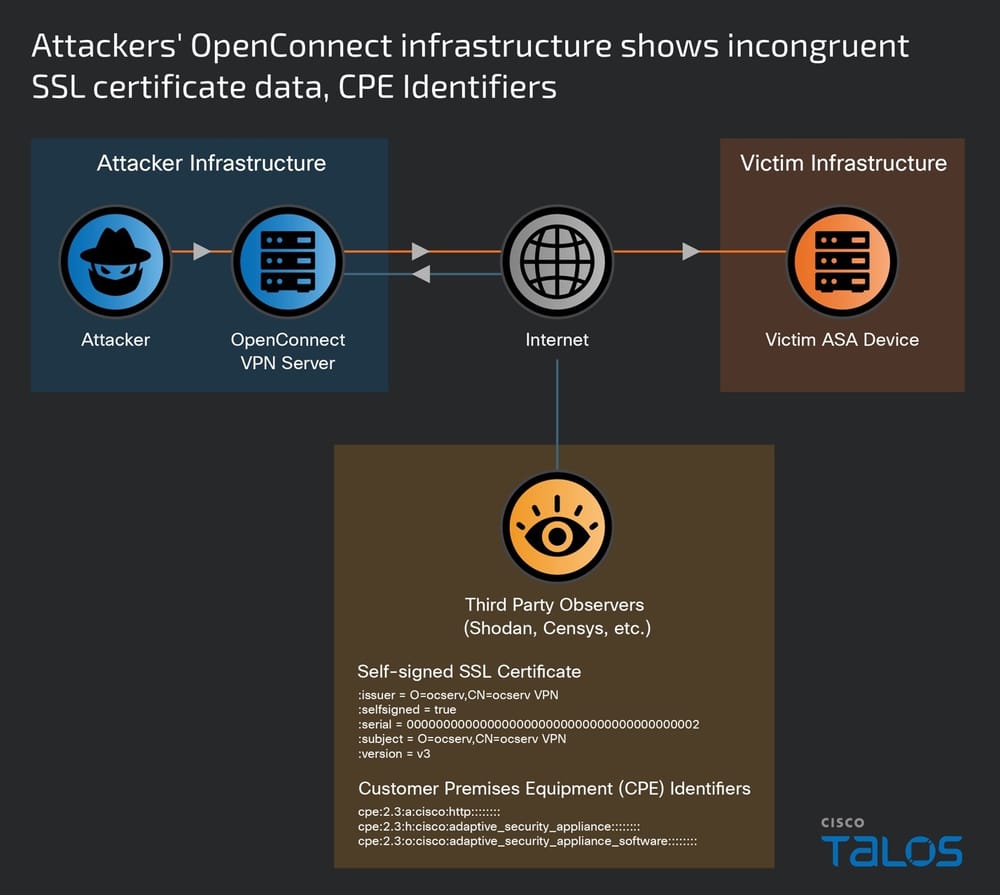
“This was obviously a malicious attempt to create a certificate with an issuer name of a trusted CA. These variants provide clear evidence that attackers in the wild are generating certificates with forged issuer attributes, and even increased their sophistication during the time frame of our study.” said the researchers.
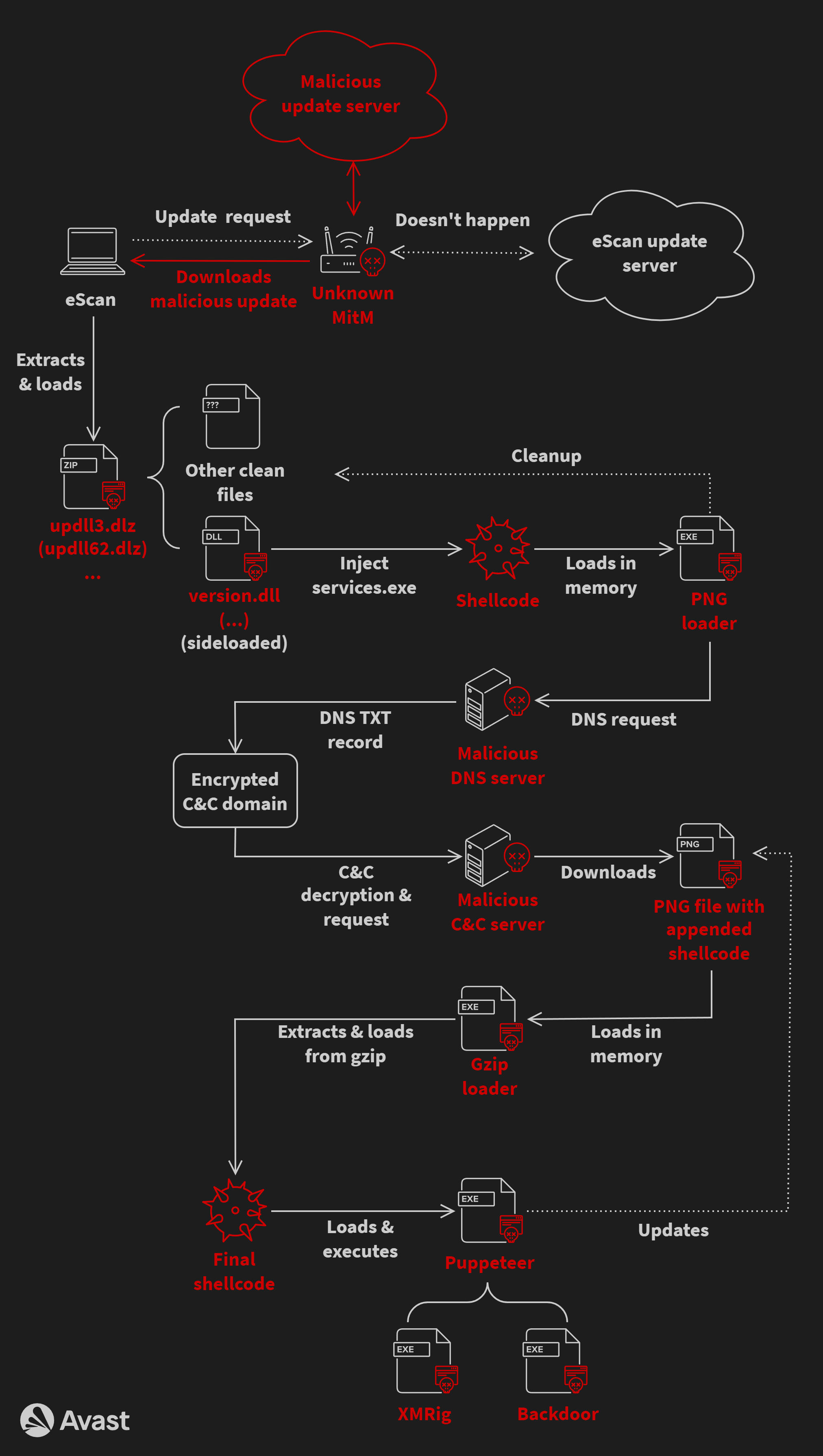
“This shows that the particular SSL man-in-the-middle attack is occurring globally in the wild. While it is possible that all of these attacks were amateur attackers individually mounting attacks (e.g. at their local coffee shop), it is certainly odd that they happened to use forged certificates with the same subject public key,” the researchers wrote. “However, this is not so unreasonable if these attacks were mounted by malware.”
The paper suggests different mitigations methods that browser vendors could implement to mitigate the cyber threat, including the adoption of HTTP Strict Transport Security, Public Key Pinning, TLS Origin Bound Certificates, and the validation of certificates with notaries.
“Our data suggest that browsers could possibly detect many of the forged certificates based on size characteristics, such as checking whether the certificate chain depth is larger than one,” the report said. “We strongly encourage popular websites, as well as mobile applications, to deploy similar mechanisms to start detecting SSL interception.”
(Security Affairs – SSL certificates, Man-In-The-Middle)