
Microsoft is warning of continuing attempts by nation-state actors and cybercriminals to exploit recently discovered vulnerabilities in the Apache Log4j library to deploy malware on vulnerable systems.
Microsoft recommends customers review their infrastructure looking for vulnerable installations, according to the experts, organizations may not realize their environments may already be compromised.
“Exploitation attempts and testing have remained high during the last weeks of December. We have observed many existing attackers adding exploits of these vulnerabilities in their existing malware kits and tactics, from coin miners to hands-on-keyboard attacks.” reads the post published by Microsoft Threat Intelligence Center (MSTIC).
Immediately after the disclosure of the first vulnerability, Microsoft warned of nation-state actors attempting to exploit the Log4Shell vulnerability in Log4j, and in the successive days, other flaws (CVE-2021-45046, CVE-2021-45105, CVE-2021-4104, and CVE-2021-44832) were discovered in the library that were exploited by threat actors in the wild.
Most of the attacks observed by the researchers are mass-scanning, coin mining, establishing remote shells, and red-team activity,
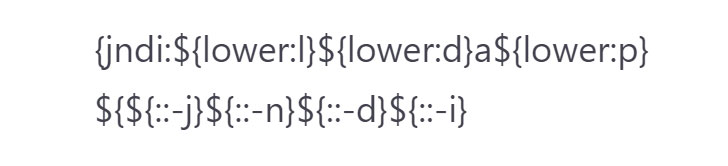
A common pattern of attack would appear in a web request log with strings like the following:

The above string can be easily identified by analyzing its components such as the presence of “jndi” (the Java Naming and Directory Interface), “ldap”, “ldaps”, “rmi”, “dns”, “iiop”, or “http.” However, attackers are adding obfuscation to these requests to evade the detection based on request analysis.
Even as the mass scanning attempts are showing no signs of letting up, efforts are underway to evade string-matching detections by obfuscating the malicious HTTP requests orchestrated to generate a web request log using Log4j that leverages JNDI to perform a request to the attacker-controlled site.
Microsoft warns of a rapid uptake of the flaw into existing botnets like Mirai and Tsunami, the company also continued to observe malicious activity performing data leakage via the vulnerability without dropping a payload.
“Microsoft has observed rapid uptake of the vulnerability into existing botnets like Mirai, existing campaigns previously targeting vulnerable Elasticsearch systems to deploy cryptocurrency miners, and activity deploying the Tsunami backdoor to Linux systems. Many of these campaigns are running concurrent scanning and exploitation activities for both Windows and Linux systems, using Base64 commands included in the JDNI:ldap:// request to launch bash commands on Linux and PowerShell on Windows.” continues Microsoft.
“Microsoft has also continued to observe malicious activity performing data leakage via the vulnerability without dropping a payload. This attack scenario could be especially impactful against network devices that have SSL termination, where the actor could leak secrets and data.”
The experts also reported the dropping of additional RATs and reverse shells by exploiting the CVE-2021-44228 in human-operated attacks. The researchers observed the use of the Cobalt Strike and PowerShell reverse shells, along with Meterpreter, njRAT (aka Bladabindi), and HabitsRAT.
The IT giant also confirmed that Webtoos DDoS malware was also deployed via the Log4Shell vulnerability.
“customers should assume broad availability of exploit code and scanning capabilities to be a real and present danger to their environments. Due to the many software and services that are impacted and given the pace of updates, this is expected to have a long tail for remediation, requiring ongoing, sustainable vigilance.” Microsoft concludes.
Follow me on Twitter: @securityaffairs and Facebook
| [adrotate banner=”9″] | [adrotate banner=”12″] |
(SecurityAffairs – hacking, Log4j)
[adrotate banner=”5″]
[adrotate banner=”13″]